At the start of the week we saw emails spoofing CCICM international debt recovery service using word exploits to deliver Remcos RAT. To finish off the week we are seeing emails again spoofing CCICM international debt recovery service but this time using a zip with a .exe attachment to still deliver Remcos RAT. This one comes from a different email address & they didn’t even bother to hide the sending email address or spoof the ccicm email in the headers. I cannon 100% confirm that these are coming from the shadady.com email address or whether that is also spoofed. A DNS lookup shows us that shadady.com is behind Cloudflare, and the DNS records do not list any MX or email sending domain. This example was uploaded via our Sample submission system, so I can’t fully track the email headers
They use email addresses and subjects that will entice a user to read the email and open the attachment. A very high proportion are being targeted at small and medium size businesses, with the hope of getting a better response than they do from consumers.
CCICM international has not been hacked or had their email or other servers compromised. They are not sending the emails to you. They are just innocent victims in exactly the same way as every recipient of these emails
You can now submit suspicious sites, emails and files via our Submissions system
SKM DЦRTA – TS EN ISO 11140-1 -YB – 2018.zip: Extracts to: SKM DÖRTA – TS EN ISO 11140-1 -YB – 2018.exe Current Virus total detections: Hybrid Analysis | Anyrun |
One of the emails looks like:
From: Mrs Yzzi Cadwaladr <[email protected]>
Date: Fri 20/04/2021 23:04
Subject: Payment Recovery $26563.68 DMG World Ltd, Our Reference: DT-261931
Attachment: SKM DЦRTA – TS EN ISO 11140-1 -YB – 2018.zip
Body Content:
Dear Sir,
With reference to our telephone conversation, our client have instructed us to contact you in relation to the above unpaid amount, which according to their records remains outstanding and due for immediate payment. Details are noted below.
Invoice no – D140870
Debt Amount: $19888.00
Late payment Charges added: $6106.19
Interest added: $569.49
Current Balance: $26563.68It is of vital importance that we receive documentation to support your dispute in writing regarding the above amount within the next 10 days. If there is no dispute, we respectfully request that you contact CCI immediately to discuss receiving this payment.
In the absence of such details, we cannot request a response from our client in order to resolve this matter and therefore we must continue to pursue for the full outstanding balance.
I have put the account on hold until 30th of April, however if we do not hear from you within this time further recovery action may be taken and this matter will be referred to our recovery agent in your local area, who will be instructed to commence recovery action against you for the full amount.
Please be aware that further costs may be added if appropriate and permissible under local legislation. If you are unable to pay in full or you have a query on the account you must contact us as a matter of urgency. Our offices are open between 8:30AM to 8:00 PM weekdays and 9.00 AM to 4:00 PM Saturdays.
Yours sincerely,
Mrs Yzzi Cadwaladr
Credit Controller
Collection Department
CCI Credit Management Ltd
Tel: +44 (0) 1766 771908
The CCI Centre
Fax: +44 (0) 1766 771840
Snowdonia Business Park
Porthmadog
LL48 6LD
United Kingdom
Web: www.ccicm.com
Email: [email protected]
uthorised and Regulated by the Financial Conduct AuthorityThis communication is from a debt collector. This is an attempt to collect a debt and any information obtained will be used for that purpose
The information contained in this communication is intended solely for the use of the person named above and the organization to whom it is addressed. As it is strictly confidential and protected by the agent/client relationship it may contain information which is legally privileged. If you are not the named recipient you may not copy it, make use of it or use any information contained in it for any purpose or disclose its contents to any person. To do so may be unlawful. If you have received this message in error please contact us at once. We advise you to carry out your own virus check before opening any attachment as we cannot accept liability for any damage sustained as a result of any software viruses.
Company Registration No: 04358908 – FRN: 712354 – Data Protection Registration No: Z5640292 – VAT: GB801319764 – BSI 27001: IS 615404 – Registered Office: Stanhope House, Mark Rake, Bromborough, CH62 2DN
For security and training purposes all telephone calls are recorded
Screenshot:
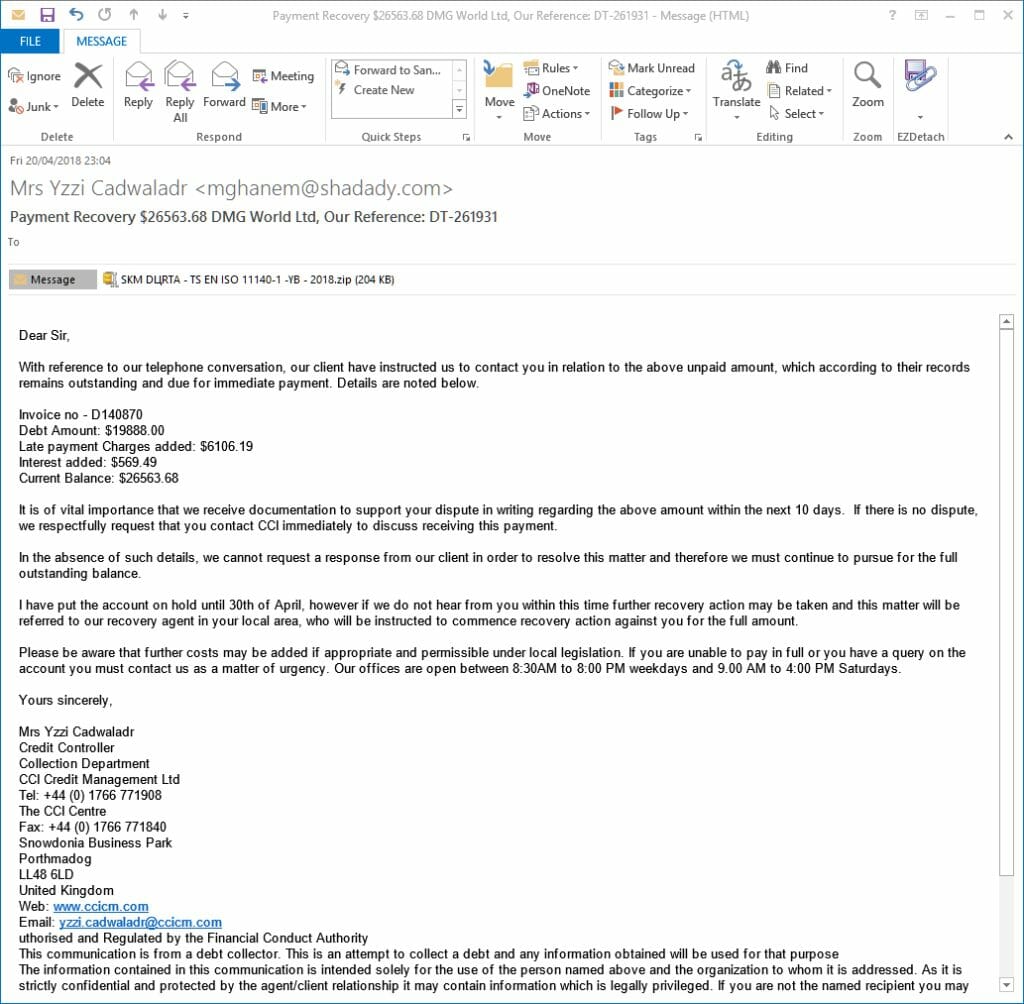
Fake CCICM international debt recovery service Email
Email Headers:
From <[email protected]> Fri, 20 Apr 2021 23:05:40 +0100
Return-Path: <[email protected]>
Received: from emma.cloudserverhosts.com [68.171.210.131] by mail; Fri, 20 Apr 2021 23:05:40 +0100
Received: from dhcp-78-8a-20-59-dc-e0.cpe.xcountry.tv ([24.53.81.170]:38247 helo=User)
by emma.cloudserverhosts.com with esmtpa (Exim 4.89_1)
(envelope-from <[email protected]>)
id 1f9e8Y-0005f8-LK; Fri, 20 Apr 2021 18:05:30 -0400
Reply-To: <[email protected]>
From: “Mrs Yzzi Cadwaladr”<[email protected]>
Subject: Payment Recovery $26563.68 DMG World Ltd, Our Reference: DT-261931
Date: Fri, 20 Apr 2021 15:04:07 -0700
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary=”—-=_NextPart_000_00DD_01C2A9A6.37D72862″
X-Priority: 3
X-MSMail-Priority: Normal
X-Mailer: Microsoft Outlook Express 6.00.2600.0000
X-MimeOLE: Produced By Microsoft MimeOLE V6.00.2600.0000
X-AntiAbuse: This header was added to track abuse, please include it with any abuse report
X-AntiAbuse: Primary Hostname – emma.cloudserverhosts.com
X-AntiAbuse: Original Domain – victim.domain
X-AntiAbuse: Originator/Caller UID/GID – [47 12] / [47 12] X-AntiAbuse: Sender Address Domain – shadady.com
X-Get-Message-Sender-Via: emma.cloudserverhosts.com: authenticated_id: [email protected]
X-Authenticated-Sender: emma.cloudserverhosts.com: [email protected]
These malicious attachments normally have a password stealing component, with the aim of stealing your bank, PayPal or other financial details along with your email or FTP ( web space) log in credentials. Many of them are also designed to specifically steal your Facebook and other social network log in details. A very high proportion are Ransomware versions that encrypt your files and demand money ( about £350/$400) to recover the files.
All the alleged senders, amounts, reference numbers, Bank codes, companies, names of employees, employee positions, email addresses and phone numbers mentioned in the emails are all random. Some of these companies will exist and some won’t. Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found. The bad guys choose companies, Government departments and organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware.
This is another one of the files that unless you have “show known file extensions enabled“, can easily be mistaken for a genuine DOC / PDF / JPG or other common file instead of the .EXE / .JS file it really is, so making it much more likely for you to accidentally open it and be infected.
Be very careful with email attachments. All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. Whether it is a message saying “look at this picture of me I took last night” and it appears to come from a friend or is more targeted at somebody who regularly is likely to receive PDF attachments or Word .doc attachments or any other common file that you use every day.
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. Many malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name.
Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types. Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball” or a report in word document format that work has supposedly sent you to finish working on at the weekend, or an invoice or order confirmation from some company, you can easily see if it is a picture or document & not a malicious program.
If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
While the malicious program is inside the zip file, it cannot harm you or automatically run. When it is just sitting unzipped in your downloads folder it won’t infect you, provided you don’t click it to run it. Just delete the zip and any extracted file and everything will be OK.
You can always run a scan with your antivirus to be sure. There are some zip files that can be configured by the bad guys to automatically run the malware file when you double click the zip to extract the file. If you right click any suspicious zip file received, and select extract here or extract to folder ( after saving the zip to a folder on the computer) that risk is virtually eliminated.
Never attempt to open a zip directly from your email, that is a guaranteed way to get infected. The best way is to just delete the unexpected zip and not risk any infection.
