I haven’t seen any examples of this Resume malware for a while now, so when this popped up in my inbox, it looked interesting enough to investigate a bit more. This is a continuation from these 3 previous posts about malware using resumes or job applications as the lure. [1] [2] [3] They have changed behaviour again since that post was written and it is time to once again update the details. ( I have only received 1 so far today that was uploaded via the submission system here.
The primary change in delivery method is the use of a password for the word doc to try to bypass antivirus filters. However there does appear to be differences in the malware itself to previous versions.
Today’s version continues to Smoke Loader /Sharik trojan which is a downloader for other malware.
An email with the subject of Website Job Application coming from Rob Meyers <[email protected]> ( probably random names) with a malicious word doc attachment delivers Smoke loader/ sharik trojan.
They are using email addresses and subjects that will scare, shock, persuade or entice a user to read the email and open the attachment. These are generally targeted at small or medium sized businesses, small charities or organisations who might not have enterprise level protections against this sort of malware delivery method. In today’s current jobs climate, it is extremely common to get resumes or job applications out of the blue. These are just generic enough and just about believable so that a busy, hardworking HR department or General Office dogsbody in a small organisation could be tempted to look at the word doc to see if the details matched the company requirements, before replying.
Remember many email clients, especially on a mobile phone or tablet, only show the Name in the From: and not the bit in <domain.com >. That is why these scams and phishes work so well.
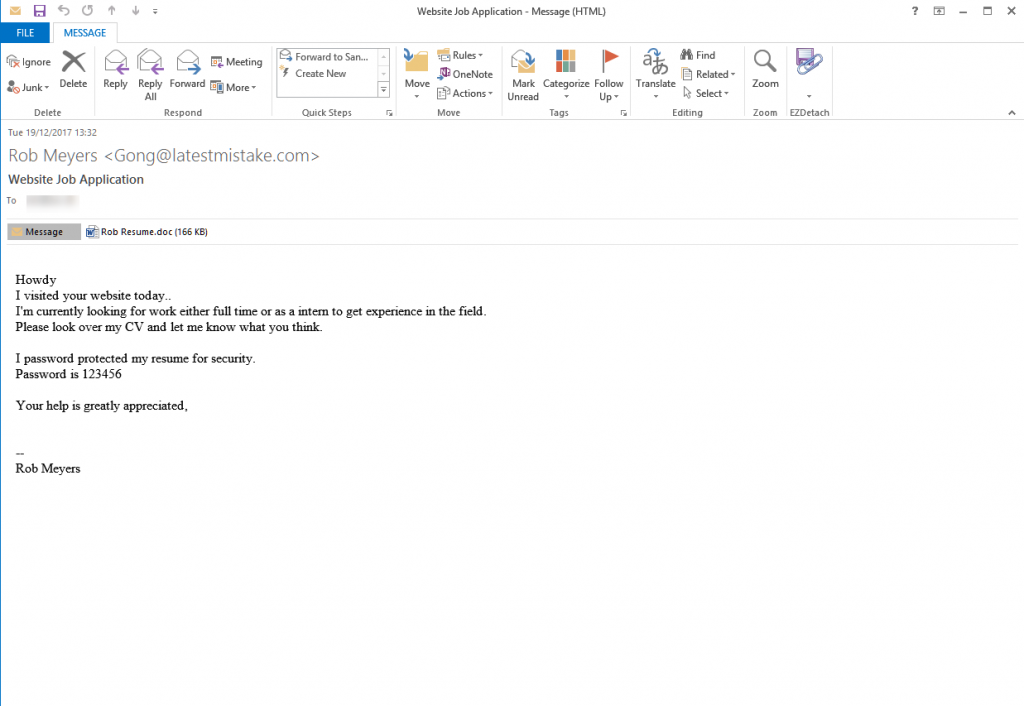
The email looks like:
From: Rob Meyers <[email protected]>
Date: Tue 19/12/2021 13:32
Subject: Website Job Application
Attachment: Rob Resume.doc
Body Content:
Howdy
I visited your website today..
I’m currently looking for work either full time or as a intern to get experience in the field.
Please look over my CV and let me know what you think.
I password protected my resume for security.
Password is 123456
Your help is greatly appreciated,
—
Rob Meyers
Screenshot:
Rob Resume.doc Current Virus total detections: Hybrid Analysis | AnyRun beta | It should be noted that this malicious word doc and the downloaded malware either has some sort of anti-analysis protection or the malware delivery site will reject connections from known sandboxes, VM analysis tools and known researcher or antivirus IP addresses. Neither of the 2 Online sandboxes / analysis tools could retrieve the downloaded malware. That had to be done manually.
They have continued with the previous behaviour of using BITS (bitsadmin.exe) to download the file instead of PowerShell. They also are still using “autoclose” in the macro so it doesn’t run until the word doc has been closed, so avoiding any obvious signs of infiltration. Also the downloaded file sleeps for a long, long time before doing anything.
This malware downloads from http://80.82.67.217/paddle.jpg which of course it not an image file but a renamed .exe (ASxas.exe) VirusTotal | Hybrid Analysis | Anyrun Beta | HA shows a further download of a bitcoin miner ( VirusTotal ) but Anyrun could not get anything despite leaving it running for 10 minutes. It is highly likely that a “genuine” victim getting this malware installed on his or her computer will get a large variety of different malware files dropped and run over an extended period of time. None of the online sandboxes or analysis tools can run for an indefinite period and completely imitate the behaviour of a real computer.
HA also shows some “interesting” connections to 107.181.246.221 ( microsoftoutlook.bit) This looks like some sort of C2 sending information,which uses a DNS system outside the standard DNS systems (Wikipedia). This either requires a browser plugin or some sort of bitcoin miner to use.
The malware IP 80.82.67.217 is “owned” by quasinetworks.com ( used to be called Ecatel) who have a somewhat debatable reputation when it comes to dealing with abuse reports [1]
This word doc looks like this:
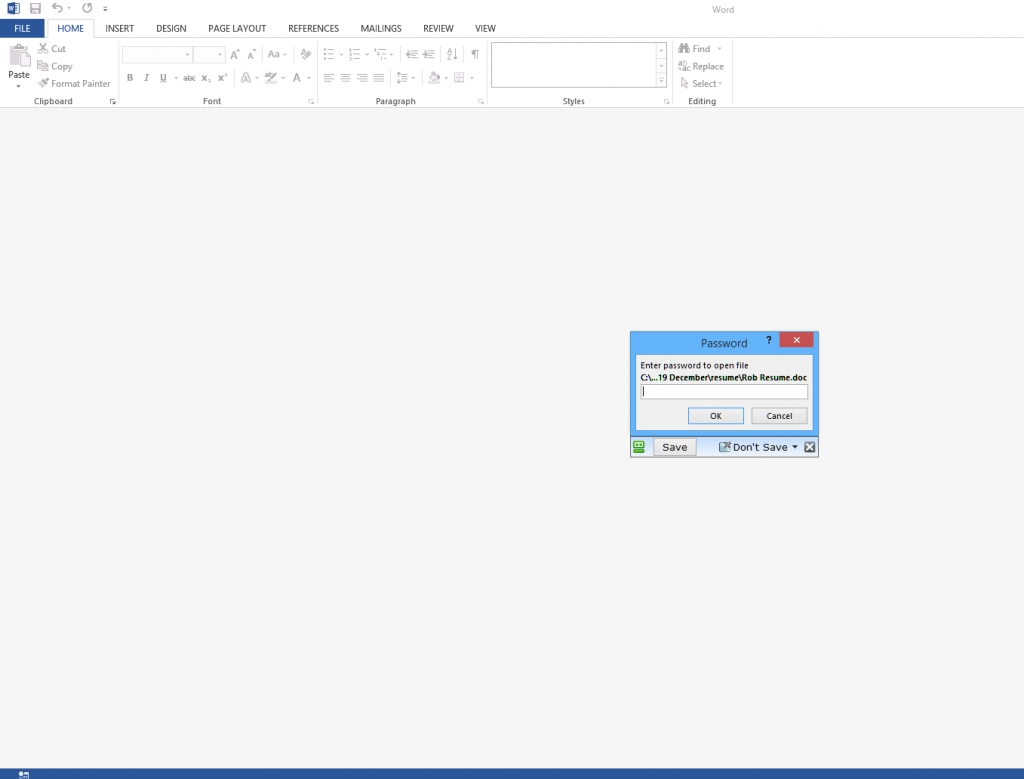
And after you input the password from the email body ( 123456) you see a typical page asking you to enable editing and then macros and content
Email Headers And Website Details:
latestmistake.com was registered in September 2021 using privacy protection via Namecheap.com as registrar. It appears to be hosted by OVH on 158.69.54.98 with SPF and DKIM authentication set up allowing it to also send emails from 66.70.229.27 ( in fact any IP address inside the 66.70.229.0/24 range). Couple this with the fact there is no website set up on the IP address , This suggests that the domain has been set up to be used in these fraud & malware spreading campaigns.
Received: from mta27.latestmistake.com (unknown [66.70.229.27])
by (removed for privacy) with ESMTP
id afba146f-e4f9-11e7-8a28-005056a84df4;
Tue, 19 Dec 2021 20:17:51 +0000 (UTC)
DKIM-Signature: v=1; a=rsa-sha1; c=relaxed/relaxed; s=bulk; d=latestmistake.com;
h=From:To:Subject:Message-ID:Date:Content-Type:MIME-Version; [email protected];
bh=sJCGggdU3v6DOdOvptJwfToQybg=;
b=J78dErzzYnfRPJrh7QMYaR3tA3k4XszVzXa3YqwbZnnOqQL4aABMjl8YZuBxqEYLibQgA44BsAjU
YQE9ilIiAWnfHs4jkUD8Yrsbrosm38+vk/r5pdIG2LuKXeKzt38YBKHHYh2RF8Kc2mmDgmtGXnI/
rfGie/an7745YvjbrlA=
DomainKey-Signature: a=rsa-sha1; c=nofws; q=dns; s=bulk; d=latestmistake.com;
b=K9EuZfxK5rrm5eiWPDI35aX3OPbCra7RGUFmYV1CWKGTwf0T1DkBpmNI1ZZJPrWjlvUuLnupCCRe
Wu66xWtJL4PQeGyezjHf0UmcuBF6iezI1CM8hYiGkaViEYfmKx1aqYK8yFCj9EZWRgleaAfJZN9/
6niKSx8lea12oL0zwiA=;
From: “Rob Meyers” <[email protected]>
To: [email protected]
Subject: Website Job Application
Message-ID: <[email protected]>
X-Priority: 3
Importance: Normal
Date: Tue, 19 Dec 2021 14:31:36 +0100
Content-Type: multipart/mixed;
boundary=”–InfrawareEmailBoundaryDepth1_2B991227–”
MIME-Version: 1.0
X-Mailer: Infraware POLARIS Mobile Mailer v2.5
Errors-To: <[email protected]>
Return-Path: <[email protected]>
All the alleged senders, companies, names of employees, phone numbers, amounts, reference numbers etc. mentioned in the emails are all innocent and are just picked at random. Some of these companies will exist and some won’t. Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found . The bad guys choose companies, Government departments and other organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
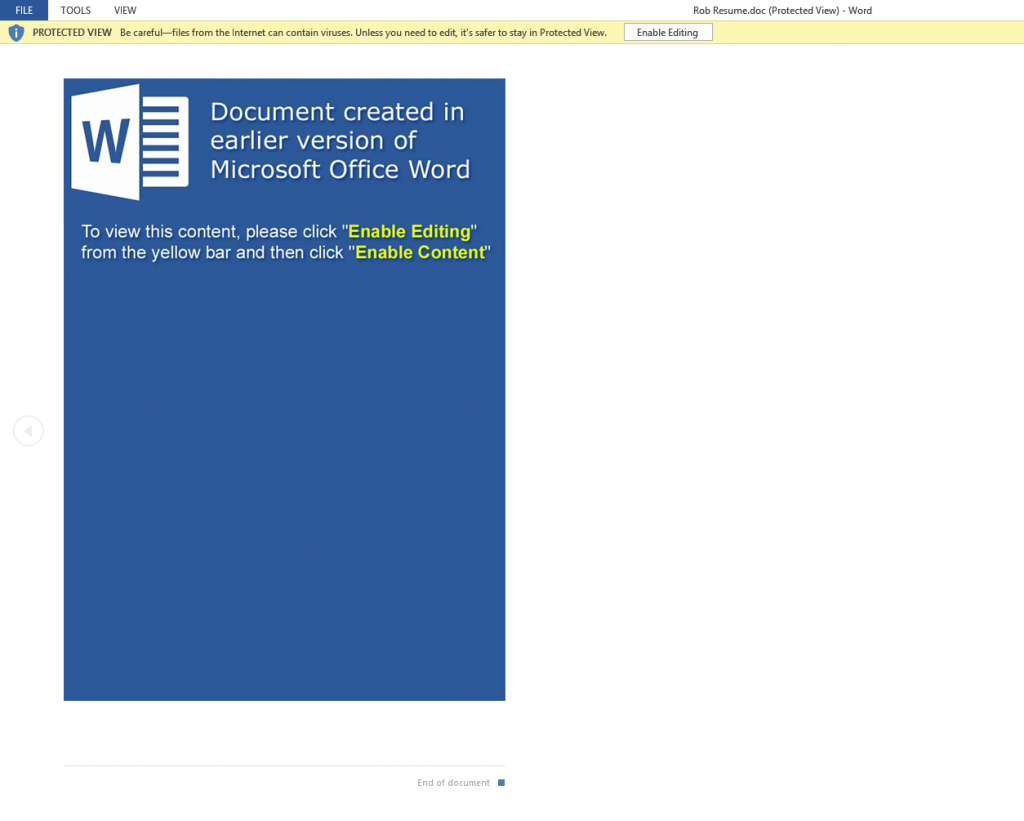
Modern versions of Microsoft office, that is Office 2010, 2013, 2016 and Office 365 should be automatically set to higher security to protect you.
By default protected view is enabled and macros are disabled, UNLESS you or your company have enabled them. If protected view mode is turned off and macros are enabled then opening this malicious word document will infect you, and simply previewing it in windows explorer or your email client might well be enough to infect you. Definitely DO NOT follow the advice they give to enable macros or enable editing to see the content.
Most of these malicious word documents either appear to be totally blank or look something like these images when opened in protected view mode, which should be the default in Office 2010, 2013, 2016 and 365. Some versions pretend to have a digital RSA key and say you need to enable editing and Macros to see the content. Do NOT enable Macros or editing under any circumstances.
What Can Be Infected By This
At this time, these malicious macros only infect windows computers. They do not affect a Mac, IPhone, IPad, Blackberry, Windows phone or Android phone.
The malicious word or excel file can open on any device with an office program installed, and potentially the macro will run on Windows or Mac or any other device with Microsoft Office installed. BUT the downloaded malware that the macro tries to download is windows specific, so will not harm, install or infect any other computer except a windows computer. You will not be infected if you do not have macros enabled in Excel or Word. These Macros do not run in “Office Online” Open Office, Libre Office, Word Perfect or any other office program that can read Word or Excel files.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware. Also please read our post about word macro malware and how to avoid being infected by them
Be very careful with email attachments. All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. It might be a simple message saying “look at this picture of me I took last night” that appears to come from a friend. It might be a scare ware message that will make you open the attachment to see what you are accused of doing. Frequently it is more targeted at somebody ( small companies etc.) who regularly receive PDF attachments or Word .doc attachments or any other common file that you use every day, for example an invoice addressed to [email protected].
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets. Many of us routinely get Word, Excel or PowerPoint attachments in the course of work or from companies that we already have a relationship with.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. A lot of malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name.
Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types. Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball”, an invoice or receipt from some company for a product or service or receive a Word doc or Excel file report that work has supposedly sent you to finish working on at the weekend, you can easily see if it is a picture or document & not a malicious program. If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
With these malformed infected word, excel and other office documents that normally contain a vba macro virus, the vital thing is do not open any office document direct from your email client or the web. Always save the document to a safe location on your computer, normally your downloads folder or your documents folder and scan it with your antivirus. Many Antiviruses do not natively detect vba macro-viruses in real time protection and you need to enable document or office protection in the settings. Do not rely on your Anti-Virus to immediately detect the malware or malicious content. DO NOT enable editing mode or enable macros
All modern versions of word and other office programs, that is 2010, 2013, 2016 and 365, should open all Microsoft office documents that is word docs, excel files and PowerPoint etc that are downloaded from the web or received in an email automatically in “protected view” that stops any embedded malware or macros from being displayed and running.
Make sure protected view is set in all office programs to protect you and your company from these sorts of attacks and do not over ride it to edit the document until you are 100% sure that it is a safe document. If the protected mode bar appears when opening the document DO NOT enable editing mode or enable macros the document will look blank or have a warning message, but will be safe.
Be aware that there are a lot of dodgy word docs spreading that WILL infect you with no action from you if you are still using an out dated or vulnerable version of word. This is a good reason to update your office programs to a recent version and stop using office 2003 and 2007.
Many of us have continued to use older versions of word and other office programs, because they are convenient, have the functions and settings we are used to and have never seen a need to update to the latest super-duper version. The risks in using older version are now seriously starting to outweigh the convenience, benefits and cost of keeping an old version going.
I strongly urge you to update your office software to the latest version and stop putting yourself at risk, using old out of date software.
