An email with the subject of FW: Important BACs documents pretending to come from Royal Bank of Scotland but actually coming from a look-a-like domain <[email protected]> with a link to malicious zip attachment containing a .js file is today’s latest spoof of a well known company, bank or public authority delivering Trickbot banking Trojan
This gang have changed behaviour today & the email contains a link to visit the fake domain to download a zip containing a .js file which in turn downloads the Trickbot banking Trojan
They are using email addresses and subjects that will scare or entice a user to read the email and open the attachment. A very high proportion are being targeted at small and medium size businesses, with the hope of getting a better response than they do from consumers.
Remember many email clients, especially on a mobile phone or tablet, only show the Name in the From: and not the bit in <domain.com >. That is why these scams and phishes work so well.
RBS has not been hacked or had their email or other servers compromised. They are not sending the emails to you. They are just innocent victims in exactly the same way as every recipient of these emails.
What has happened is that the criminals sending these have registered various domains that look like genuine Bank domains. Normally there are 3 or 4 newly registered domains that imitate the bank or some message sending service that can easily be confused with a legitimate organisation in some way that send these
So far we have only found 1 domain today
- rbsdocs.co.uk
As usual they are registered via Godaddy as registrar and hosted by Godaddy on ip 160.153.162.130 but the emails are being sent via host Europe 85.93.88.125
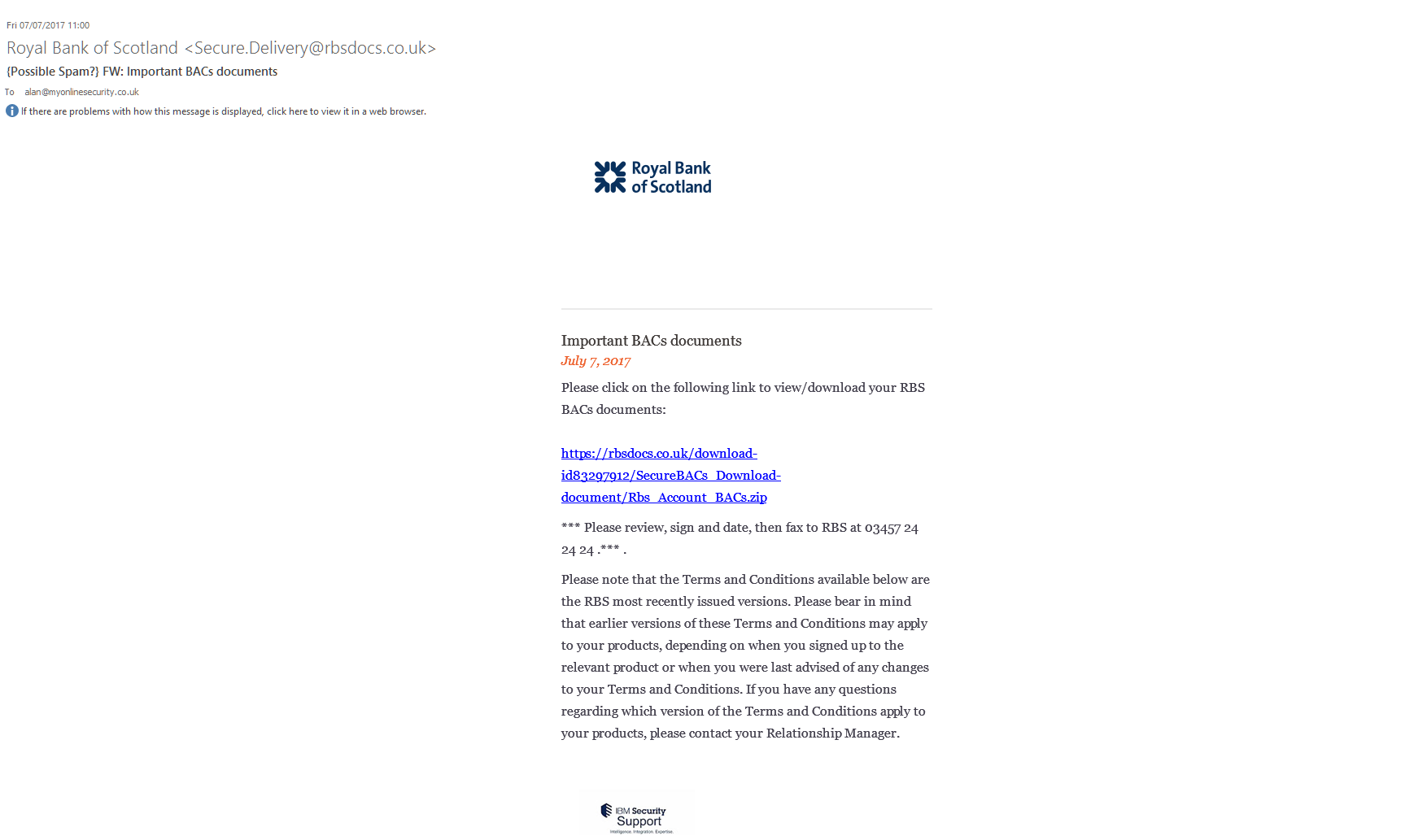
The email looks like:
From: Royal Bank of Scotland <[email protected]>
Date: Fri 07/07/2020 11:00
Subject: Secure email message
Attachment: FW: Important BACs documents
Body content:
Important BACs documents
July 7, 2020
Please click on the following link to view/download your RBS BACs documents:
https://rbsdocs.co.uk/download-id83297912/SecureBACs_Download-document/Rbs_Account_BACs.zip
*** Please review, sign and date, then fax to RBS at 03457 24 24 24 .*** .
Please note that the Terms and Conditions available below are the RBS most recently issued versions. Please bear in mind that earlier versions of these Terms and Conditions may apply to your products, depending on when you signed up to the relevant product or when you were last advised of any changes to your Terms and Conditions. If you have any questions regarding which version of the Terms and Conditions apply to your products, please contact your Relationship Manager.
Remember: We will never ask you to provide your full Security Number or Password. Worried your accounts may have been accessed by someone other than you – or think you have responded to a suspicious e-mail? Call us immediately on 0845 600 8212 (Minicom 0845 900 5960). When calling from abroad please dial +44 131 317 4597 (Minicom +44 141 308 8045).Calls may be recorded. Maximum call charge from a BT landline is 4p per minute. Calls from other networks may vary
© 2005-2021 The Royal Bank of Scotland plc
Screenshot:
Email Headers:
| IP | Hostname | City | Region | Country | Organisation |
|---|---|---|---|---|---|
| 85.93.88.125 | static-ip-85-93-88-125.inaddr.ip-pool.com | Hoest | North Rhine-Westphalia | DE | AS8972 Host Europe GmbH |
Received: from static-ip-85-93-88-125.inaddr.ip-pool.com ([85.93.88.125]:49335 helo=rbsdocs.co.uk)
by knight.knighthosting.co.uk with esmtp (Exim 4.89)
(envelope-from <[email protected]>)
id 1dTQKn-0003o4-H8
for [email protected]; Fri, 07 Jul 2021 11:18:01 +0100
DKIM-Signature: v=1; a=rsa-sha1; c=relaxed/relaxed; s=key; d=rbsdocs.co.uk;
h=Mime-Version:Date:To:Subject:From:Content-Type:Message-ID;
bh=+u/ywkYX/NxB54XNOHf00xmXsmg=;
b=VHGqaVibeDJqUmvfftzcttXB7Y0ZZpTRuGQxCIPfk/miKHoUm0Y+0JkMY3QINMTCmOgf8bbchfBw
WTfR4GDAcf2SK04a55DFNaOINT0gvKxwsGbRzhLQA9unRMX9rDglPduTC+Hhi0SZN3OarW03B8zJ
gBCNdPgUjiTBBp07yMyGB8DOQz54AC1W+jAja0bKkrO2d80FepptM+w6x/UDWSIx9IU/eJfd9GT1
nBDFXzfxwH9K6KCi/ffT4PGgRdvO6A74bl4N+UW/xQYEMEeF5cVBtM55D9i5gqvC79vpm1KoDAzl
/9lR/xSK7p1M2GhOpfZI0ySY5V8OxwpMeqOmfg==
Received: by rbsdocs.co.uk id hbtft2mqbj8b for <[email protected]>; Fri, 7 Jul 2021 05:59:41 -0400 (envelope-from <[email protected]>)
Mime-Version: 1.0
Date: Fri, 7 Jul 2021 05:59:41 -0400
To: [email protected]
Subject: FW: Important BACs documents
From: “Royal Bank of Scotland” <[email protected]>
Content-Type: multipart/alternative;
boundary=4d77cabe479eefc5ae9abf19893a1e2c
Message-ID: <[email protected]>
Note: Only the final IP address outside of your network in the Received: fields can be trusted as others can be spoofed
Rbs_Account_BACs.js Current Virus total detections: Payload Security shows a download from http://mutfakdolabisitesi.com/grandsergiostalls.png which of course is not an image file but a renamed .exe file that gets renamed to qkY5ijY.exe and autorun ( VirusTotal)
All the alleged senders, companies, names of employees, phone numbers, amounts, reference numbers etc. mentioned in the emails are all innocent and are just picked at random. Some of these companies will exist and some won’t. Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found . The bad guys choose companies, Government departments and other organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
Please read our How to protect yourselves page (https://myonlinesecurity.co.uk/how-to-protect-yourself-and-tighten-security/) for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware. Also please read our post about word macro malware and how to avoid being infected by them
Be very careful with email attachments. All of these emails use Social engineering (https://en.wikipedia.org/wiki/Social_engineering_(security)) tricks to persuade you to open the attachments that come with the email. It might be a simple message saying “look at this picture of me I took last night” that appears to come from a friend. It might be a scare ware message that will make you open the attachment to see what you are accused of doing. Frequently it is more targeted at somebody ( small companies etc.) who regularly receive PDF attachments or Word .doc attachments or any other common file that you use every day, for example an invoice addressed to [email protected].
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets. Many of us routinely get Word, Excel or PowerPoint attachments in the course of work or from companies that we already have a relationship with.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. A lot of malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name.
Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types. Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball”, an invoice or receipt from some company for a product or service or receive a Word doc or Excel file report that work has supposedly sent you to finish working on at the weekend, you can easily see if it is a picture or document & not a malicious program. If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
With these malformed infected word, excel and other office documents that normally contain a vba macro virus, the vital thing is do not open any office document direct from your email client or the web. Always save the document to a safe location on your computer, normally your downloads folder or your documents folder and scan it with your antivirus. Many Antiviruses do not natively detect vba macro-viruses in real time protection and you need to enable document or office protection in the settings. Do not rely on your Anti-Virus to immediately detect the malware or malicious content. DO NOT enable editing mode or enable macros
All modern versions of word and other office programs, that is 2010, 2013, 2016 and 365, should open all Microsoft office documents that is word docs, excel files and PowerPoint etc that are downloaded from the web or received in an email automatically in “protected view” (https://support.office.com/en-gb/article/What-is-Protected-View-d6f09ac7-e6b9-4495-8e43-2bbcdbcb6653) that stops any embedded malware or macros from being displayed and running.
Make sure protected view is set in all office programs to protect you and your company from these sorts of attacks and do not over ride it to edit the document until you are 100% sure that it is a safe document. If the protected mode bar appears when opening the document DO NOT enable editing mode or enable macros the document will look blank or have a warning message, but will be safe.
Be aware that there are a lot of dodgy word docs spreading that WILL infect you with no action from you if you are still using an out dated or vulnerable version of word. This is a good reason to update your office programs to a recent version and stop using office 2003 and 2007.
Many of us have continued to use older versions of word and other office programs, because they are convenient, have the functions and settings we are used to and have never seen a need to update to the latest super-duper version. The risks in using older version are now seriously starting to outweigh the convenience, benefits and cost of keeping an old version going.
I strongly urge you to update your office software to the latest version and stop putting yourself at risk, using old out of date software.
