Apple Care pretending to come from Apple <[email protected]> is one of the latest phish attempts to steal your Apple Account and your Bank, credit card and personal details.
This one only wants your personal details, Apple log in details and your credit card and bank details. Many of them are also designed to specifically steal all your other email, facebook and other social network log in details as well.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware.
The original email looks like this It will NEVER be a genuine email from Apple or any other company so don’t ever click the link in the email. If you do it will lead you to a website that looks at first glance like the genuine Apple website but you can clearly see in the address bar, that it is fake. Some versions of this phish will ask you fill in the html ( webpage) form that comes attached to the email.
| Apple/iCloud ID [redacted] This is the final notice to inform you as of 31 – July – 2021 that you have not yet reviewed your Apple ID information. Under “Know your Customer” legislation Apple Inc is required by law to carry out a verification of your information, failure to complete this validation will result in deletion of your Apple ID within the next three days. Please continue to » Login to your iTunes ID To cancel the deletion of your iCloud proceed to your Apple ID information before the deadline. Case Ticket ID: #R2TIK141284747 Regards, Apple Help Inc. |
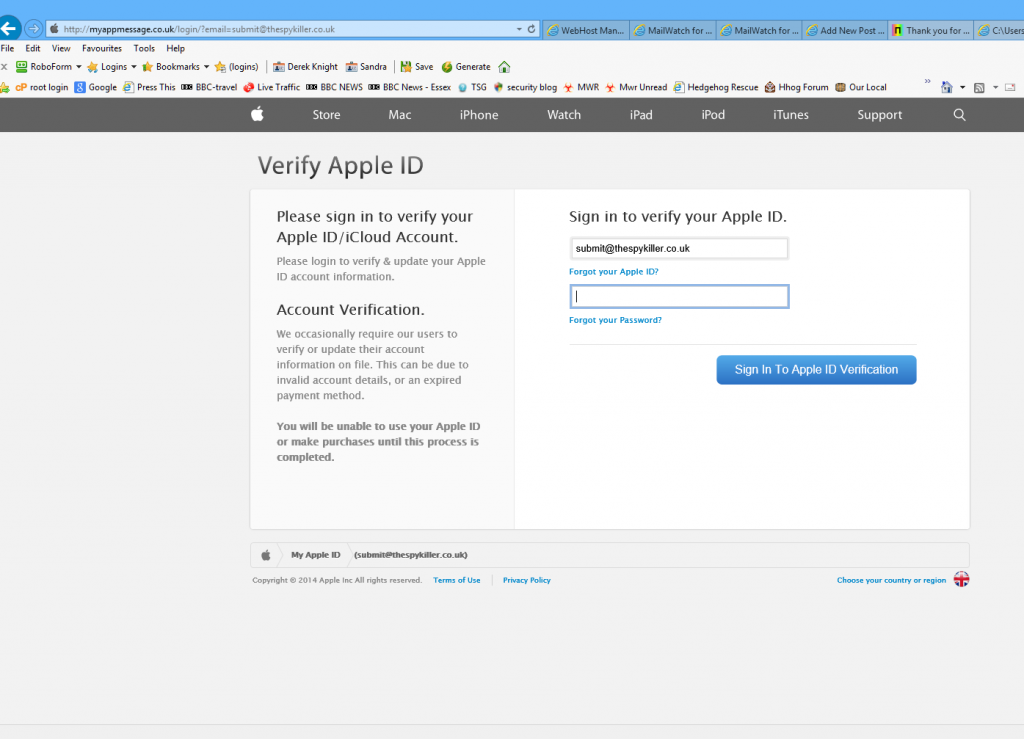
If you follow the link you see a webpage looking like :
The actual site this sends you to is http://applesurveillance.com/account/[email protected] which can very easily be mistaken for a genuine Apple site. To make it even worse, the phishers have gone to the effort of setting up the domain properly and are using an email address to send from “Apple <[email protected]> ” which has the correct domainkeys and SPF records so it doesn’t look like spam and will be allowed past most spam filters
They have also set up the applesurveillance.com site so that it appears to a security researcher or investigator that the account has been suspended by the hosting provider, when it actually is live when you put any email address into the url
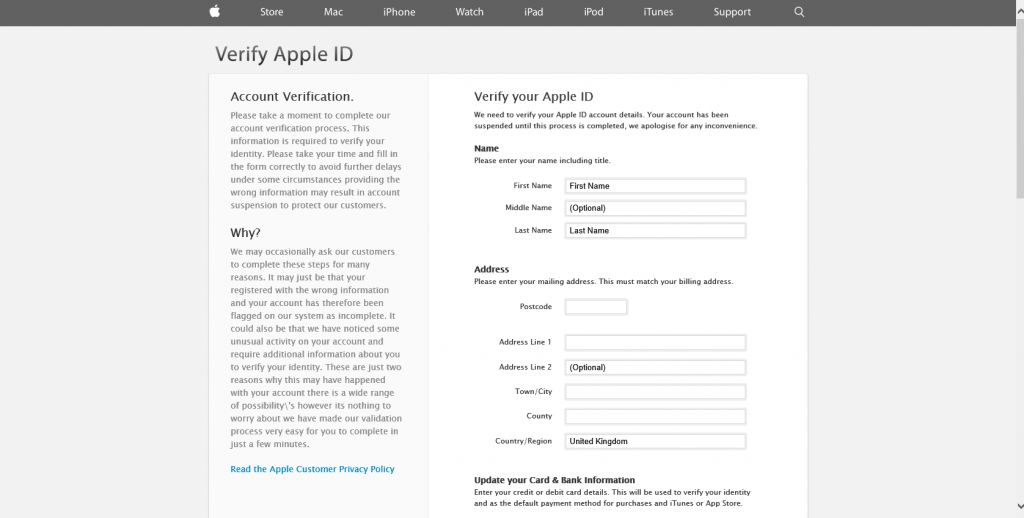
When you fill in your user name and password you get a page looking very similar to this one ( split into sections), where the phishers try to validate your details to make sure that you are entering “genuine ” information. They make sure that the bank account numbers have the correct number of digits and that the credit card numbers have the correct number of digits and format.

All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. Whether it is a message saying “look at this picture of me I took last night” and it appears to come from a friend or is more targeted at somebody who regularly is likely to receive PDF attachments or Word .doc attachments or any other common file that you use every day. Or whether it is a straight forward attempt, like this one, to steal your personal, bank, credit card or email and social networking log in details.
Be very careful when unzipping them and make sure you have “show known file extensions enabled“, And then look carefully at the unzipped file. If it says .EXE then it is a problem and should not be run or opened.
