We are seeing a fairly large Ursnif /Gozi /ISFB campaign hitting the UK since Yesterday. The criminals are using the theme of Brexit which is very topical in UK ( and the rest of Europe) at the moment. There are numerous subjects all with Brexit somewhere in the subject line and there is a link to a google docs page that downloads the malware file.
Some subjects I have seen include:
- Brexit 2019
- Brexit 29/03/2019
- Brexit 29-03-2019
- Brexit | 29-03-2019
- Brexit Barometer
- Brexit
These are coming from dozens ( or even hundreds) of different email addresses and IP addresses all from 1 hosting company using the IP range of 193.233.30.* This appears to be a server based in Russia, mgnhost.ru AS202423 PE Viktor Tyurin. All the email addresses pass authentication and the majority of the sending domains have been registered for several years.
All the domains are using name servers on DOMAINCONTROL.COM which suggests that there has been a compromise on the name server system to redirect the legitimate domains to the Russian hosting servers and consequently involve them in this & other malware distribution campaigns
You can now submit suspicious sites, emails and files via our Submissions system
The link in the email is to where a file Brexit_Barometer.exe is delivered to you. Unusually all the links are identical. We frequently see numerous different Google docs links.
Brexit_Barometer.exe Current Virus total detections: Hybrid Analysis | Anyrun |
Another researcher on Twitter has posted this info about the Ursnif binary
Release : ‘DEC 10 2018’ Version : 3.0.667 Server : 12 ID : 10000 Encryption key : EkS3rrEz4bwL1yeK C2 Server : akamaicln[.]com
One of the emails looks like:
From: service <[email protected]>
Date: Mon 10/12/2018 16:29
Subject: Brexit 2019
Body content:
Introducing the Brexit Barometer
With the “meaningful vote” in the UK Parliament on Tuesday the 11th and the final EU summit on the 13th and 14th of December, you should be prepared for all possible outcomes given there is a strong possibility the vote will fail in the UK parliament.
Our looks at the potential impact we think Brexit could have on the pound. As Theresa May tours the country in the lead up to the “meaningful vote”, we can expect to see significant volatility in Sterling in the event of a ‘disorderly Brexit”.
Handling volatility in the market
We’ve outlined some ways you can stay up-to-date with the market so that you can transfer at a time that works best for you.
o Set up a personalised Rate Alert – be alerted the minute the market reaches your desired rate
o Keep an eye out for our regular Brexit updates so you can keep up with the latest announcements
o Sign up for our Market Watch so you can receive daily updates on market movements
Contact us
If you’d like to discuss your situation with us in more detail, please contact us and our team will be happy to help.
The details expressed in this transmission and accompanying documents are for information purposes only and are not intended as a solicitation for funds or a recommendation to trade. HiFX Europe Limited accepts no liability whatsoever for any loss or damages suffered through any act or omission taken as a result of reading or interpreting any of the above information. HiFX Europe Limited is authorised by the Financial Conduct Authority under the Payment Services Regulations 2017, registration 462444, for the provision of payment services. HiFX Europe Limited is also a registered MSB with HM Revenue & Customs. Registration number: 12131222. HiFX is a limited company registered in England and Wales. Registered number: 3517451. Registered office: Maxis 1, Western Road, Bracknell, Berkshire, RG12 1RT.
Please note that by unsubscribing you will no longer receive marketing messages from HiFX. However to maintain your HiFX account you will receive service messages from time to time.
Screenshot:
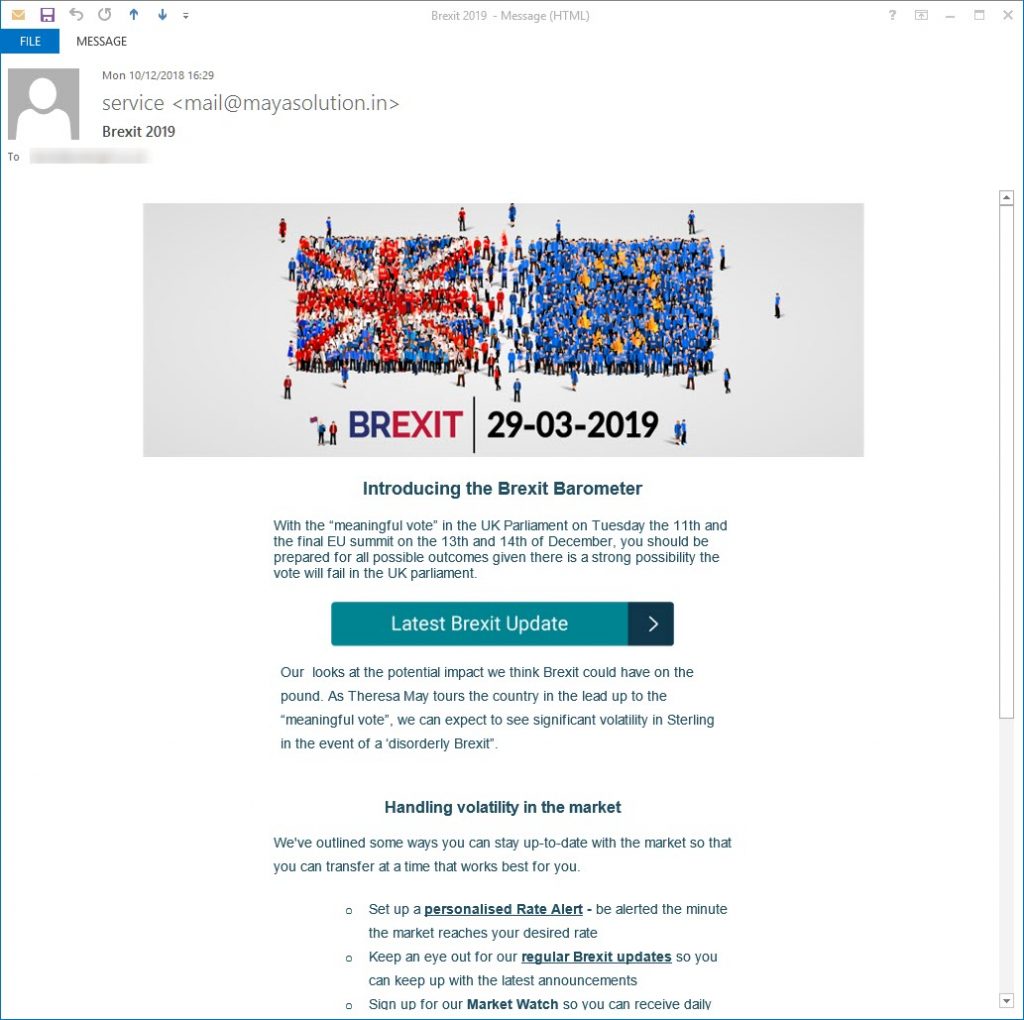
Fake Brexit email
All the links in the email except the “Latest Brexit Update” link which delivers the malware go to a spam test service
These malicious attachments normally have a password stealing component, with the aim of stealing your bank, PayPal or other financial details along with your email or FTP ( web space) log in credentials. Many of them are also designed to specifically steal your Facebook and other social network log in details. A very high proportion are Ransomware versions that encrypt your files and demand money ( about £350/$400) to recover the files.
All the alleged senders, amounts, reference numbers, Bank codes, companies, names of employees, employee positions, email addresses and phone numbers mentioned in the emails are all random. Some of these companies will exist and some won’t. Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found.
The bad guys choose companies, Government departments and organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware.
This is another one of the files that unless you have “show known file extensions enabled“, can easily be mistaken for a genuine DOC / PDF / JPG or other common file instead of the .EXE / .JS file it really is, so making it much more likely for you to accidentally open it and be infected.
Be very careful with email attachments. All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. Whether it is a message saying “look at this picture of me I took last night” and it appears to come from a friend or is more targeted at somebody who regularly is likely to receive PDF attachments or Word .doc attachments or any other common file that you use every day.
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. Many malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name. Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types.
Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball” or a report in word document format that work has supposedly sent you to finish working on at the weekend, or an invoice or order confirmation from some company, you can easily see if it is a picture or document & not a malicious program.
If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
While the malicious program is inside the zip file, it cannot harm you or automatically run. When it is just sitting unzipped in your downloads folder it won’t infect you, provided you don’t click it to run it. Just delete the zip and any extracted file and everything will be OK. You can always run a scan with your antivirus to be sure. There are some zip files that can be configured by the bad guys to automatically run the malware file when you double click the zip to extract the file.
If you right click any suspicious zip file received, and select extract here or extract to folder ( after saving the zip to a folder on the computer) that risk is virtually eliminated. Never attempt to open a zip directly from your email, that is a guaranteed way to get infected. The best way is to just delete the unexpected zip and not risk any infection.
