I am hearing about a return of the fake UKPC parking charge appeals scam which has been quiet for about 1 year. At this time I don’t have a copy of the email that was received by the victim, only the link that was in it. I assume the email will be very similar to the ones described in these 2 posts [1] [2].
UKPC are a nationwide company that controls parking on private property throughout many parts of the UK. They do not ( as far as I can tell) control on street parking on behalf of any Local Authority in the UK. There is a lot of information on the internet suggesting UKPC are a scam or less scrupulous company that regularly breaks the law and issues non enforceable penalty notices, for spurious “offences”. I am not going to get into the argument over private parking companies sending out penalty notices here. This post is alerting to a current malware delivery campaign using the UKPC logo & imitation of their website to scam recipients & steal banking details.
These campaigns are generally very well done & use sites that resemble strongly the genuine UKPC Appeals site ukpcappeals.co.uk.
The current domain being used in this malware delivery scam is ukpcappeals.org which is a look-a-like, typo-squatted or other domain that can easily be misidentified, mistaken or confused with the genuine site. The criminals behind this scam have made it much more difficult for researchers and antivirus companies to investigate this delivery method easily. Each IP and computer only gets 1 attempt at contacting the site and downloading the zip file, then you get a 403 forbidden message.
You can now submit suspicious sites, emails and files via our Submissions system
UKPC has not been hacked or had their email or other servers compromised. They are not sending the emails to you.
The email link was to http://7csx.ukpcappeals.org/files/data_info/checkinfo.php where you see a page looking like this. After inserting the captcha and press view photos a randomly named zip file is downloaded
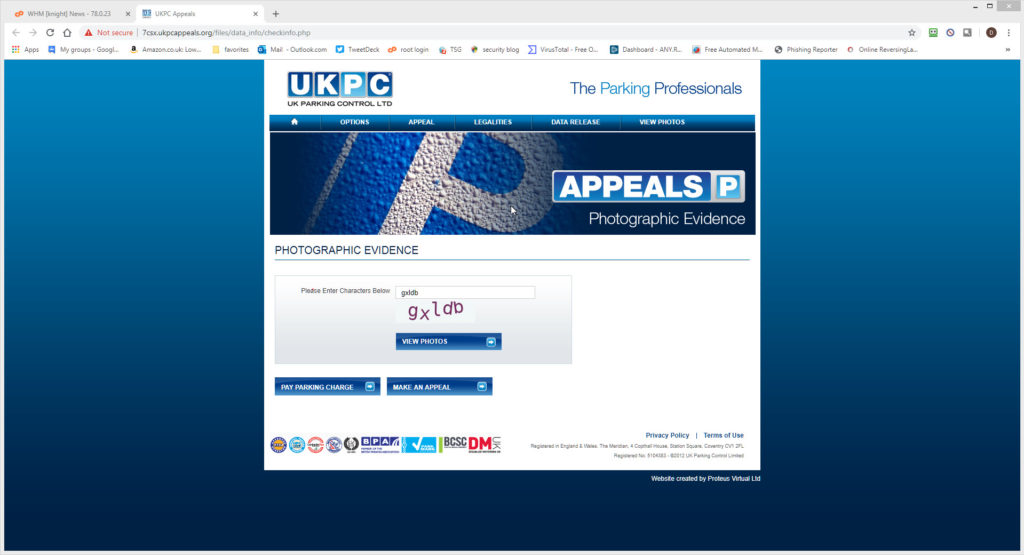 Fake Typo-squatted UKPC appeals site
Fake Typo-squatted UKPC appeals site
78397.zip : Extracts to: TVTT_CAM92741.vbs Current Virus total detections: AnyrunApp | which is the gootkit downloader. This vbs calls out to http://51.254.160.193/media/report_201904 where it downloads 2 files. The first a pdf which is displayed to the victim and the second a .exe which automatically runs in the background, so stealing the victims banking details.
report242.exe ( VirusTotal)
This is another one of the files that unless you have “show known file extensions enabled“, can easily be mistaken for a genuine DOC / PDF / JPG or other common file instead of the .vbs scripting file it really is, so making it much more likely for you to accidentally open it and be infected.
These malicious attachments normally have a password stealing component, with the aim of stealing your bank, PayPal or other financial details along with your email or FTP ( web space) log in credentials. Many of them are also designed to specifically steal your Facebook and other social network log in details. A very high proportion are Ransomware versions that encrypt your files and demand money ( about £350/$400) to recover the files.
All the alleged senders, amounts, reference numbers, Bank codes, companies, names of employees, employee positions, email addresses and phone numbers mentioned in the emails are all random. Some of these companies will exist and some won’t.
Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found. The bad guys choose companies, Government departments and organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware.
Be very careful with email attachments. All of these emails use Social engineering (https://en.wikipedia.org/wiki/Social_engineering_(security)) tricks to persuade you to open the attachments that come with the email. Whether it is a message saying “look at this picture of me I took last night” and it appears to come from a friend or is more targeted at somebody who regularly is likely to receive PDF attachments or Word .doc attachments or any other common file that you use every day.
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. Many malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name.
Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types. Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball” or a report in word document format that work has supposedly sent you to finish working on at the weekend, or an invoice or order confirmation from some company, you can easily see if it is a picture or document & not a malicious program.
If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
While the malicious program is inside the zip file, it cannot harm you or automatically run. When it is just sitting unzipped in your downloads folder it won’t infect you, provided you don’t click it to run it. Just delete the zip and any extracted file and everything will be OK. You can always run a scan with your antivirus to be sure.
There are some zip files that can be configured by the bad guys to automatically run the malware file when you double click the zip to extract the file. If you right click any suspicious zip file received, and select extract here or extract to folder ( after saving the zip to a folder on the computer) that risk is virtually eliminated. Never attempt to open a zip directly from your email, that is a guaranteed way to get infected. The best way is to just delete the unexpected zip and not risk any infection.
Website Details
Address Lookup
| canonical name | ukpcappeals.org. |
| aliases | |
| addresses | 47.91.93.231 |
Domain Whois Record
Queried whois.publicinterestregistry.net with “ukpcappeals.org“…
Domain Name: UKPCAPPEALS.ORG
Registry Domain ID: D402200000010144677-LROR
Registrar WHOIS Server: whois.namesilo.com
Registrar URL: www.namesilo.com
Updated Date: 2021-04-24T14:00:52Z
Creation Date: 2021-04-24T13:59:45Z
Registry Expiry Date: 2020-04-24T13:59:45Z
Registrar Registration Expiration Date:
Registrar: Namesilo, LLC
Registrar IANA ID: 1479
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.4805240066
Reseller:
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: serverTransferProhibited https://icann.org/epp#serverTransferProhibited
Registrant Organization: See PrivacyGuardian.org
Registrant State/Province: AZ
Registrant Country: US
Name Server: A.DNSPOD.COM
Name Server: B.DNSPOD.COM
Name Server: C.DNSPOD.COM
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form https://www.icann.org/wicf/)
>>> Last update of WHOIS database: 2020-05-15T14:22:11Z <<<
Network Whois Record
Queried whois.arin.net with “n ! NET-47-91-64-0-1“…
NetRange: 47.91.64.0 – 47.91.95.255
CIDR: 47.91.64.0/19
NetName: ALICLOUD-GM
NetHandle: NET-47-91-64-0-1
Parent: AL-3 (NET-47-88-0-0-1)
NetType: Reassigned
OriginAS: AS45102
Customer: ALICLOUD-GM (C06961501)
RegDate: 2021-04-20
Updated: 2021-04-20
Comment: 1.For AliCloud IPR Infringement and Abuse Claim, please use below link with browser to report: https://intl.aliyun.com/report
Comment:
Comment: 2.For Alibaba.com and Aliexpress.com’s IPR Infringement , please use below link with browser to report: https://ipp.alibabagroup.com
Comment:
Comment: 3.For Alibaba.com and Aliexpress.com’s Abuse, please send email to those two mail lists to report: [email protected] and [email protected]
Comment:
Comment: 4. For network issue, please send email to this mail list: [email protected]
Ref: https://rdap.arin.net/registry/ip/47.91.64.0
CustName: ALICLOUD-GM
Address: Westendstrabe 28, 60325 Frankfurt am Main
City: Frankfurt
StateProv:
PostalCode:
Country: DE
RegDate: 2020-04-20
Updated: 2021-04-20
Ref: https://rdap.arin.net/registry/entity/C06961501
OrgTechHandle: ALIBA-ARIN
OrgTechName: Alibaba NOC
OrgTechPhone: +1-408-748-1200
OrgTechEmail: [email protected]
OrgTechRef: https://rdap.arin.net/registry/entity/ALIBA-ARIN
OrgAbuseHandle: NETWO4028-ARIN
OrgAbuseName: Network Abuse
OrgAbusePhone: +1-408-785-5580
OrgAbuseEmail: [email protected]
OrgAbuseRef: https://rdap.arin.net/registry/entity/NETWO4028-ARIN
OrgNOCHandle: ALIBA-ARIN
OrgNOCName: Alibaba NOC
OrgNOCPhone: +1-408-748-1200
OrgNOCEmail: [email protected]
OrgNOCRef: https://rdap.arin.net/registry/entity/ALIBA-ARIN
Address Lookup
| canonical name | securecheck256.com. |
| aliases | |
| addresses | 51.38.154.26 |
Domain Whois Record
Queried whois.internic.net with “dom securecheck256.com“…
Domain Name: SECURECHECK256.COM
Registry Domain ID: 2344067859_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.webnic.cc
Registrar URL: http://www.webnic.cc
Updated Date: 2021-12-19T08:42:23Z
Creation Date: 2020-12-17T15:24:50Z
Registry Expiry Date: 2020-12-17T15:24:50Z
Registrar: Web Commerce Communications Limited dba WebNic.cc
Registrar IANA ID: 460
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +603.89966788
Domain Status: clientDeleteProhibited https://icann.org/epp#clientDeleteProhibited
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: clientUpdateProhibited https://icann.org/epp#clientUpdateProhibited
Name Server: NS31.CLOUDNS.NET
Name Server: NS32.CLOUDNS.NET
Name Server: NS33.CLOUDNS.NET
Name Server: NS34.CLOUDNS.NET
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/
>>> Last update of whois database: 2021-05-16T02:09:28Z <<<
Queried whois.webnic.cc with “securecheck256.com“…
Domain Name: securecheck256.com
Registry Domain ID: 2344067859_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.webnic.cc
Registrar URL: webnic.cc
Updated Date: 2020-12-17T15:24:49Z
Creation Date: 2019-12-17T15:24:51Z
Registrar Registration Expiration Date: 2021-12-17T15:24:50Z
Registrar: WEBCC
Registrar IANA ID: 460
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +60.389966799
Domain Status: clientUpdateProhibited https://www.icann.org/epp#clientUpdateProhibited
Domain Status: clientTransferProhibited https://www.icann.org/epp#clientTransferProhibited
Domain Status: clientDeleteProhibited https://www.icann.org/epp#clientDeleteProhibited
Registry Registrant ID: Not Available From Registry
Registrant Name: Joshua Huff
Registrant Organization: Joshua Huff
Registrant Street: 126 Heatherleigh
Registrant City: Cooksville
Registrant State/Province: ON
Registrant Postal Code: L5A1V9
Registrant Country: CA
Registrant Phone: +1.9052108430
Registrant Phone Ext:
Registrant Fax: +1.9052108430
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: Not Available From Registry
Admin Name: Joshua Huff
Admin Organization: Joshua Huff
Admin Street: 126 Heatherleigh
Admin City: Cooksville
Admin State/Province: ON
Admin Postal Code: L5A1V9
Admin Country: CA
Admin Phone: +1.9052108430
Admin Phone Ext:
Admin Fax: +1.9052108430
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID: Not Available From Registry
Tech Name: Joshua Huff
Tech Organization: Joshua Huff
Tech Street: 126 Heatherleigh
Tech City: Cooksville
Tech State/Province: ON
Tech Postal Code: L5A1V9
Tech Country: CA
Tech Phone: +1.9052108430
Tech Phone Ext:
Tech Fax: +1.9052108430
Tech Fax Ext:
Tech Email: [email protected]
Name Server: NS31.CLOUDNS.NET
Name Server: NS32.CLOUDNS.NET
Name Server: NS33.CLOUDNS.NET
Name Server: NS34.CLOUDNS.NET
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2021-12-17T15:24:49Z <<<
Network Whois Record
Queried whois.ripe.net with “-B 51.38.154.26“…
% Information related to ‘51.38.154.24 – 51.38.154.27’
% Abuse contact for ‘51.38.154.24 – 51.38.154.27’ is ‘[email protected]’
inetnum: 51.38.154.24 – 51.38.154.27
netname: OVH_177596012
country: PL
descr: Failover Ips
org: ORG-GS206-RIPE
admin-c: OTC12-RIPE
tech-c: OTC12-RIPE
status: LEGACY
mnt-by: OVH-MNT
created: 2021-05-04T18:31:27Z
last-modified: 2021-05-04T18:31:27Z
source: RIPE
organisation: ORG-GS206-RIPE
org-name: OU IPHOSTER
org-type: OTHER
address: Randla 13-201
address: 10315 Tallinn
address: EE
e-mail: [email protected]
phone: +372.8804544
abuse-c: ACRO15706-RIPE
mnt-ref: OVH-MNT
mnt-by: OVH-MNT
created: 2019-08-04T07:06:03Z
last-modified: 2021-04-25T00:06:15Z
source: RIPE
role: OVH PL Technical Contact
address: OVH Sp. z o. o.
address: Ul. Szkocka 5 lok. 1
address: 54-402 Wroclaw
address: Poland
e-mail: [email protected]
admin-c: OK217-RIPE
tech-c: GM84-RIPE
nic-hdl: OTC12-RIPE
abuse-mailbox: [email protected]
notify: [email protected]
mnt-by: OVH-MNT
created: 2019-09-16T16:09:56Z
last-modified: 2021-10-30T11:40:58Z
source: RIPE
% Information related to ‘51.38.0.0/16AS16276’
route: 51.38.0.0/16
origin: AS16276
mnt-by: OVH-MNT
created: 2019-03-07T09:21:14Z
last-modified: 2021-03-07T09:21:14Z
source: RIPE
IOC:
Main object- “TVTT_CAM92741.vbs”
sha256 9ac5e0c4f834625fd336131d48812afda6c0e34c27cb390c924b3679985d66c5
sha1 9f2da5974abc77e792b4c540cd9bd64e8e1a91f0
md5 89c449ea3ddc6fb191ed83ade968bd87
Dropped executable file report242.exe
MD5 92037C20192404AB292FB4418FD933A4
SHA1 329FF54DB14D33503EB7C1D9C698AADD6837397B
SHA256 266A0E2E04E82B42D5DF30C70E32D58AEA042EEF7C87AF1B5CD64239F71C0FC5
Report242.pdf
MD5 3C0F58DA0900D2DA8C77CA3DE8476AB4
SHA1 0D5ED7EA200475F2CB82520F9C6641B460EC84AF
SHA256 E41A310DC5CBBD2FCBDD4EF0E5AD81F0D724C31514ACC7A2219FE5ABE9A4CF5C
DNS requests
domain securecheck256.com
domain analyticagent.com
Connections
ip 51.38.154.26
ip 51.254.160.193
ip 52.200.159.57
ip 2.16.106.152
HTTP/HTTPS requests
url http://51.254.160.193/media/download/201904/report242
url http://51.254.160.193/media/report_201904
url https://securecheck256.com/rbody32
url https://securecheck256.com/rbody320
