Another malware campaign using malformed RTF files involving Microsoft Office Equation Editor exploits to extract or drop a zip file from an embedded ole object containing the payload and an “innocent” lure doc to be displayed. Today it looks like CVE-2017-8570. The payload today is Formbook
This campaign is almost identical to the Azorult campaign I detailed a few days ago. With the same Gondi.doc ( with the code for a phishing site in it ) & using saver.scr as the payload file. This is either the same criminal gang involved in both malware campaign or the 2 different criminals are using the same “off the shelf” exploit kit and just changing the final payload. Whichever turns out to be correct illustrates the overlap between different malware campaigns.
This has the look & smell of Threadkit” exploit kit, which is an “off the shelf” kit that just about any Skiddie, low skilled miscreant or criminal can purchase for very little money & just follow the simple instructions to change the payload. Proofpoint has a post about it from early last year, that describes the kit in the form it used then. To my eyes the criminals behind it have updated the kit somewhat since that post was made.
This is quite an involved, devious chain of delivery which after opening the word doc ( RTF) attachment to the email it very quickly partially opens & then immediately closes and extracts the contents of a zip containing a Fake Word doc & the malware payload.
It then displays the fake word doc in place of the original RTF doc attachment, that in this case is the source code of a phishing HTML page. ( previous versions have been fake invoices or order docs.) and silently runs the payload without you realising anything has happened.
All you think has happened is ” Oh Hell Word has crashed again ” which is not unusual and automatically re-opens itself. You do get a very quick flash of a warning or alert about linked files, but somehow the criminals have managed to bypass the usual Word inbuilt protections & download/ drop and run the files without user interaction. This should have been fixed with an update to all supported versions of Microsoft Office starting In July 2017 and subsequent office updates.
Note: I have only run this malware on an online sandbox, that deliberately has lower security settings, so malware payloads can be easily retrieved. It is very possible that a real computer that is fully updated will not be as vulnerable to this exploit & malware delivery method and will require user interaction, clicking yes or allow to several warning prompts.
However we know that lots of consumers & small businesses and even some larger corporations, charities, Government departments etc. do not routinely update or upgrade Office to recent versions. I still frequently see old, unsupported versions of Office remaining in use. I even see Office XP & 2003 very frequently. All versions prior to Office 2010 are vulnerable to this & many other exploits.
The July 2017 Update for Office 2007 should have fixed this one but I wouldn’t 100% guarantee it because Office 2007 stopped getting security updates in October 2017. We have seen continual refinements to the various Equation editor exploits and without your office programs being updated, we cannot guarantee that older updates will fully protect you.
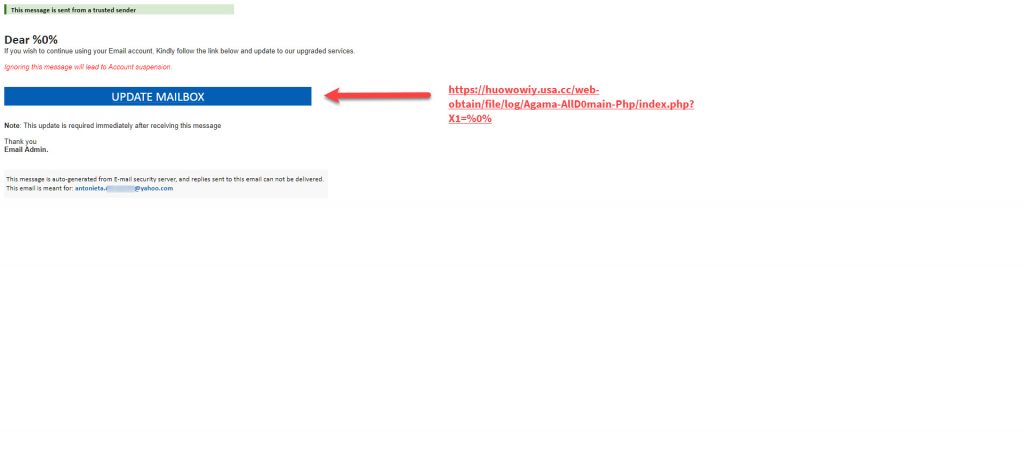
You can see the fake word doc contents in the video on Anyrun. I have converted the html code to display the “phishing page” that I think the criminals intended to be downplayed instead of the code, hoping to also steal your details that way, if the Formbook payload got blocked on the computer. The domain in the link “https://huowowiy.usa.cc/web-obtain/file/log/Agama-AllD0main-Php/index.php?X1=%0%” does not appear to exist, so either hasn’t yet been created or has already been removed by the free domain name providers.
A quick look up in Virus Total does show this url was previously used in a phishing scam in Late September 2018. Although this domain was previously removed does not mean it cannot be re-used. We have previously frequently seen free providers & many other domain registrars that remove “bad” domains, but only block the use for a certain amount of time, not permanently. This is why we often see the same “bad” domains popping up in phishing or malware campaigns every few months or years.
They are using email addresses and subjects that will scare or entice a user to read the email and open the attachment. A very high proportion are being targeted at small and medium size businesses, with the hope of getting a better response than they do from consumers.
Remember many email clients, especially on a mobile phone or tablet, only show the Name in the From: and not the bit in <domain.com >. That is why these scams and phishes work so well.
Invoice_PL.doc Current Virus total detections: AnyrunApp | Hybrid Analysis |
This malware word doc/ rtf extracts kulebiaka.ZiP (VirusTotal) that displays Gondi.doc ( a harmless lure doc) VirusTotal and the Formbook payload saver.scr Virustotal |
C2: “http://www.skylod.com/wa/”
You can now submit suspicious sites, emails and files via our Submissions system
The email looks like:
From: Kiki Sun <[email protected]>
Date: Fri 01/02/2019 23:08
Subject: RE: SHIPPING DOCUMENTS FOR PI9465
Attachment: Invoice_PL.doc
Body content:
Good day.
Attached herewith Commercial Invoice, Packing list and B/L copy No.: PI9465 / NFT1833
SHIPPING SCHEDULE FIXED AS BELOW:
ETD POL: 1/23rd
ETA POD: 3/8th
For any question, please do not hesitate to contact us.
Best regards,
Kiki Sun (VIP Customer Service Team)
Ningbo STAXX Material Handling Equipment
ADD: 1F, Main building 10, No. 688 Jinda Road, Yinzhou District, Ningbo, China 315000
Phone: +86-574-89218530
Email: [email protected]
P.S: Please resend your email if no reply from us within 2 days. Thanks for your cooperation!
STAXX main PIC:
Export Director: Thomas Wang [email protected]
VIP Customer Manager: Katrina Zhan [email protected]
After-sale Service Team: Doris Wang [email protected]
Parts Manager: Tony Zhou [email protected]
Engineer-Business Development
Screenshot:
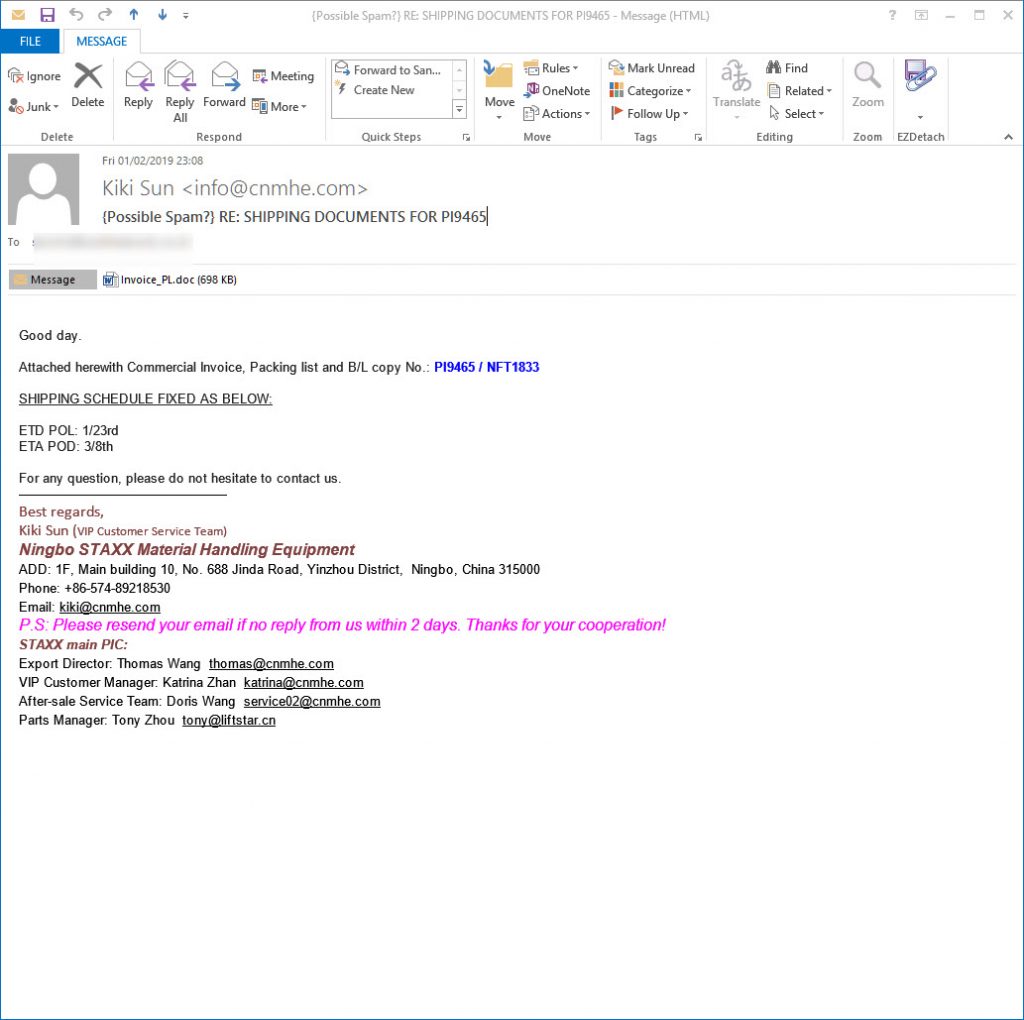
All the alleged senders, companies, names of employees, phone numbers, amounts, reference numbers etc. mentioned in the emails are all innocent and are just picked at random. Some of these companies will exist and some won’t.
Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found . The bad guys choose companies, Government departments and other organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
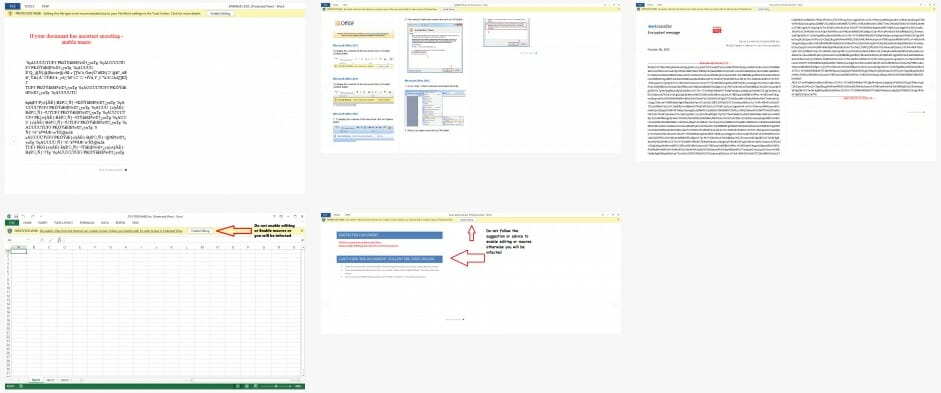
This email attachment contains what appears to be a genuine word doc or Excel XLS spreadsheet with either a macro script or an embedded OLE object that when run will infect you.
Modern versions of Microsoft office, that is Office 2010, 2013, 2016 and Office 365 should be automatically set to higher security to protect you.
By default protected view is enabled and macros are disabled, UNLESS you or your company have enabled them. If protected view mode is turned off and macros are enabled then opening this malicious word document will infect you, and simply previewing it in windows explorer or your email client might well be enough to infect you. Definitely DO NOT follow the advice they give to enable macros or enable editing to see the content.
Most of these malicious word documents either appear to be totally blank or look something like these images when opened in protected view mode, which should be the default in Office 2010, 2013, 2016 and 365. Some versions pretend to have a digital RSA key and say you need to enable editing and Macros to see the content. Do NOT enable Macros or editing under any circumstances.
What can be infected by this
At this time, these malicious macros only infect windows computers. They do not affect a Mac, IPhone, IPad, Blackberry, Windows phone or Android phone. The malicious word or excel file can open on any device with an office program installed, and potentially the macro will run on Windows or Mac or any other device with Microsoft Office installed.
BUT the downloaded malware that the macro tries to download is windows specific, so will not harm, install or infect any other computer except a windows computer. You will not be infected if you do not have macros enabled in Excel or Word. These Macros do not run in “Office Online” Open Office, Libre Office, Word Perfect or any other office program that can read Word or Excel files.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware. Also please read our post about word macro malware and how to avoid being infected by them
Be very careful with email attachments. All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. It might be a simple message saying “look at this picture of me I took last night” that appears to come from a friend.
It might be a scare ware message that will make you open the attachment to see what you are accused of doing. Frequently it is more targeted at somebody ( small companies etc.) who regularly receive PDF attachments or Word .doc attachments or any other common file that you use every day, for example an invoice addressed to [email protected].
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets. Many of us routinely get Word, Excel or PowerPoint attachments in the course of work or from companies that we already have a relationship with.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. A lot of malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name. Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types.
Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball”, an invoice or receipt from some company for a product or service or receive a Word doc or Excel file report that work has supposedly sent you to finish working on at the weekend, you can easily see if it is a picture or document & not a malicious program. If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
With these malformed infected word, excel and other office documents that normally contain a vba macro virus, the vital thing is do not open any office document direct from your email client or the web. Always save the document to a safe location on your computer, normally your downloads folder or your documents folder and scan it with your antivirus.
Many Antiviruses do not natively detect vba macro-viruses in real time protection and you need to enable document or office protection in the settings. Do not rely on your Anti-Virus to immediately detect the malware or malicious content. DO NOT enable editing mode or enable macros
All modern versions of word and other office programs, that is 2010, 2013, 2016 and 365, should open all Microsoft office documents that is word docs, excel files and PowerPoint etc that are downloaded from the web or received in an email automatically in “protected view” that stops any embedded malware or macros from being displayed and running.
Make sure protected view is set in all office programs to protect you and your company from these sorts of attacks and do not over ride it to edit the document until you are 100% sure that it is a safe document. If the protected mode bar appears when opening the document DO NOT enable editing mode or enable macros the document will look blank or have a warning message, but will be safe.
Be aware that there are a lot of dodgy word docs spreading that WILL infect you with no action from you if you are still using an out dated or vulnerable version of word. This is a good reason to update your office programs to a recent version and stop using office 2003 and 2007.
Many of us have continued to use older versions of word and other office programs, because they are convenient, have the functions and settings we are used to and have never seen a need to update to the latest super-duper version. The risks in using older version are now seriously starting to outweigh the convenience, benefits and cost of keeping an old version going.
I strongly urge you to update your office software to the latest version and stop putting yourself at risk, using old out of date software.
IOC:
Main object- “Invoice_PL.doc”
sha256 3a606edcb90bd8ccd3927f521a2615bde5bf7a672277dd5885a56bdd560b952e
sha1 96e9b8441a6b508ff39b1137a111ea9d0d04ffe8
md5 fd2f453f03892e2ee83f024704b8e204
Dropped zip
kulebiaka.ZiP
0b95e26f9577bf5e87a7fedb68f640309d0750de9f29dcd14d5a7e2a3ef14515
944470607838aaa0517f0891c28b3375
ffeae7fd114da2ca5e7fbf1071423153e76813d0
Dropped executable file
C:\Users\admin\AppData\Local\Temp\saver.scr
580fc153ada0162e121f8f6d74acfa4a44333fa0f75d4c5d968f50f95adff7cd
9f28ecab2578dd8f6b4b012a0a083ac2
dd75021b31d9db1f920bb488d91a126bac7f10fb
sha256 C:\Users\admin\AppData\Local\Temp\sqlite3.dll 16574f51785b0e2fc29c2c61477eb47bb39f714829999511dc8952b43ab17660
Displayed Lure
Gondi.doc
80ae0226822b684927280c63ca9f4e683c121fa62715e02909decc298c03b506
6291d5a22fce652360616bd330e07082
46901354d7929e8e5e7c777640ab5a3f42784406
DNS requests
domain www.skylod.com
domain www.texefeja2u.biz
domain www.aboutlives.today
domain www.polidizajn.net
domain www.mirzaianhardesty.com
domain www.linkdoors-design.com
domain www.tv16366.info
domain www.theknollslife.com
domain www.blockchainassetsroundtable.com
domain www.nmzjo.info
domain www.betturka.store
domain www.per-colator.com
domain www.ferpi-es.com
domain www.mortalcapitalism.com
domain www.truehearthospice.info
domain www.lalightsmusic.com
Connections
ip 123.56.244.28
ip 192.64.115.176
ip 104.16.97.202
ip 91.195.240.240
ip 184.168.221.57
HTTP/HTTPS requests
url http://www.linkdoors-design.com/wa/
url http://www.skylod.com/wa/?DXFTJ=4v4zjVwXCgUhvUQEF8jBQegLqvW+jDeGWAiwLvaoNiVJFn7AHBOayqRZs97SC+lNyT6yvg==&Jt7=XPv4sVZH
url http://www.linkdoors-design.com/wa/?Jt7=XPv4sVZH&DXFTJ=uMHxjEPCOs7ob/yRzi84w6Cs/nsH+FGRRg0vC5cEbYiVinywhuIglsne6IpKVX12IbYBvQ==&sql=1
url http://www.theknollslife.com/wa/?DXFTJ=IK8/dmpwokt7ZfA9iaOleDEvjQ8cx0nWiBObZ12uOhcKdhxpEXwFqPnUqJDWd0bqpHNcjQ==&Jt7=XPv4sVZH&sql=1
url http://www.theknollslife.com/wa/
url http://www.per-colator.com/wa/?DXFTJ=DnQpVlzugqf3P+aAzz3PIJNdDSa5JG4rnjx0Wo7+ox5kloto2jiqXCa20ya+G212MwWlnw==&Jt7=XPv4sVZH&sql=1
url http://www.per-colator.com/wa/
url http://www.truehearthospice.info/wa/?Jt7=XPv4sVZH&DXFTJ=4ZgT0FgCy2lVOtV91FzW7tlA5BHGrsZCYGOxHlEvmvs4pAcMAKmcSuvhvGayeMdiSJ2q5w==&sql=1
url http://www.truehearthospice.info/wa/
url http://www.skylod.com/wa/
url http://www.skylod.com/wa/?DXFTJ=4v4zjVwXCgUhvUQEF8jBQegLqvW+jDeGWAiwLvaoNiVJFn7AHBOayqRZs97SC+lNyT6yvg==&Jt7=XPv4sVZH&sql=1
url http://www.linkdoors-design.com/wa/?Jt7=XPv4sVZH&DXFTJ=uMHxjEPCOs7ob/yRzi84w6Cs/nsH+FGRRg0vC5cEbYiVinywhuIglsne6IpKVX12IbYBvQ==
url http://www.theknollslife.com/wa/?DXFTJ=IK8/dmpwokt7ZfA9iaOleDEvjQ8cx0nWiBObZ12uOhcKdhxpEXwFqPnUqJDWd0bqpHNcjQ==&Jt7=XPv4sVZH
url http://www.per-colator.com/wa/?DXFTJ=DnQpVlzugqf3P+aAzz3PIJNdDSa5JG4rnjx0Wo7+ox5kloto2jiqXCa20ya+G212MwWlnw==&Jt7=XPv4sVZH
url http://www.truehearthospice.info/wa/?Jt7=XPv4sVZH&DXFTJ=4ZgT0FgCy2lVOtV91FzW7tlA5BHGrsZCYGOxHlEvmvs4pAcMAKmcSuvhvGayeMdiSJ2q5w==
