A slight change to the usual Locky downloaders today with an email with the subject of We could not deliver your parcel, #551196 ( random numbers) pretending to come from FedEx Standard Overnight with a malicious word doc downloading Locky.
Other subjects include ( all with random numbers) :
- Problem with parcel shipping, ID: 417224026
- Shipment delivery problem #76863765563
- Problems with item delivery, n.67734337
- Courier was unable to deliver the parcel, ID1662562769788
- Unable to deliver your item, #4613214
- We could not deliver your parcel, 667016878
Update 14 November 2021: I am getting a steady wave of these again this morning. The malicious word doc with macros tries to connect to decidedlyev.top/ll/ldd.php 46.22.220.32 which is currently giving a 404 page not found. I am getting that 404 on all the other sites on that server / IP that have previously known to have been used to spread Locky over the last week or so
Update2: This afternoon’s version connects to but as previously I get a 404. I don’t know whether it needs the referrer from the macro / powershell or whether it is geo IP specific or whether the site is down.
Update 16 November 2021: still getting loads overnight . Still using still getting 404 on manual attempt to connect. Does it need a special refer or is it Geo IP specific or have they messed up and there is no malware payload. I am reliably informed that it needs a specific refer to get the locky malware via the php route. However it can be obtained via procuratorkn.top/ll/232334.exe ( VirusTotal) (Payload Security)
Update 19 November 2021: After getting some well needed education from Matthew Mesa ( a threat researcher at Proofpoint) I have finally managed to work out how to deal with these new Locky downloaders. The Locky malware gang have decided to up the ante over the last 2 weeks or so and do their best to block many researchers and antiviruses, along with the common online sandboxes and analysing systems from getting the malware payload.
Today’s version of this daily email with word docs containing macros connects to http://essentialmm.top/ll/ldd.php which actually downloads. If you try to go to ldd.php using a browser or wget, you will get a 404 or other not found / blocked / unavailable message.
You need to use the specific user agent they embed inside the macro as shown in the payload security report.[ Mozilla/4.0 (compatible; Win32; WinHttp.WinHttpRequest.5) ] You also need an IP address from the range or country being targeted.
I don’t know why, but I always have problems using Wget on windows , although I can use it perfectly on a Linux server from the command line. I instead use Firefox with a user agent switcher plugin & have this locky user agent as the option to use. I also use a proxy plugin so I can switch countries, when Locky & other malware insist on specific country IP ranges.
Update 21 November 2021: still using http://essentialmm.top/ll/ldd.php which actually downloads http://essentialmm.top/ll/6255.exe (VirusTotal on Word doc) (VT on .exe) (Payload Security word ) ( Payload Security.exe)
Update 23 November 2021: usual fedex.doc ( virustotal) now using http://sacrificery.top/ll/ldd.php which actually downloads http://sacrificery.top/ll/566.exe ( VirusTotal) ( Payload Security) MALWR shows the typical Locky behaviour and aesir file extension on encrypted files C2 http://95.46.114.205/information.cgi
Update 24 November 2021: still using http://sacrificery.top/ll/ldd.php which actually downloads http://sacrificery.top/ll/77.exe ( VirusTotal) ( VirusTotal) ( Payload Security)
Update 26 November 2021: Word malware Macro still trying to contact http://sacrificery.top/ll/ldd.php ( 46.22.220.32 ) ( VirusTotal on URL ) which actually downloads http://sacrificery.top/ll/66.exe ( VirusTotal) Currently this site fails in DNS lookups with no DNS server listed for it ( they were using Cloudflare DNS but that has been stopped and have in the past used dnspod.com DNS services.) but I have kept a record of last IP address for it and that gives me the malware daily without fail. There is no doubt that many other victims will have the DNS record in a cache and are still at risk from this .
Update 28 November 2021: usual fedex.doc ( VirusTotal) contacts http://triumphantul.top/2/ldd.php ( 46.22.220.32 )( payload Security ) which actually downloads http://triumphantul.top/2/23.exe ( VirusTotal) (Payload Security)
Update 11 December 2021: After a 2 week break I am getting these again. Still using http://triumphantul.top/2/ldd.php but have changed IP address and hosting company ( 185.101.218.162 )( payload Security ) which actually downloads http://triumphantul.top/2/565.exe ( VirusTotal) (Payload Security) MALWR C2 http://176.121.14.95/checkupdate None of the online sandboxes were actually able to connect to the download site or get the Locky Osiris ransomware. I had to examine the macro manually and do it that way.
This is a confusing change, where Locky has recently been and is concurrently using zip files with either a .VBS, .WSF or .JS scripting file inside the zip. The email template being used is more normally used by a different malware / ransomware spreading criminal gang, who send FedEx failed to deliver emails every day
I have only received 1 copy of this so fat this morning, but a quick search on MALWR and Payload Security show they originally started yesterday. The website listed as the malware download site seems down at time of posting ( from UK ) but the malware download was available via Payload Security. None of the online sandboxes show any of the usual Locky file encryption actions, but the reports clearly show the typical Locky behaviour contacting a known Locky C2 as well as a new one.
It turns out that I did receive several of these yesterday that went straight into quarantine on the server. They were interspaced with the more typical nemucod zip versions which also arrived regularly during the day. I should have looked more closely, but only looked at the email subject line in the quarantine list and didn’t pay enough attention, otherwise I would have caught this change earlier. We are more used to seeing Locky with a mass malspam with dozens if not hundreds of copies received in a very short space of time. It is very unusual to only get 1 or 2 copies at a time, spread out throughout the day.
They are using email addresses and subjects that will scare or entice a user to read the email and open the attachment. A very high proportion are being targeted at small and medium size businesses, with the hope of getting a better response than they do from consumers.
FedEx has not been hacked or had their email or other servers compromised. They are not sending the emails to you. They are just innocent victims in exactly the same way as every recipient of these emails.
The email looks like:
From: FedEx Standard Overnight <[email protected]>
Date: Wed 09/11/2021 07:50
Subject: We could not deliver your parcel, #551196
Attachment: FedEx.doc
Body Content:
Hello,
We could not deliver your item. Please, download Delivery Label attached to this email.
Kaja Helscher – Area Manager FedEx , CA
Regards
Screenshot:
9 November 2021: FedEx.doc Current Virus total detections: Payload Security shows a download from http://perfectionbm.top/ll/ldd.php which is saved as 0.7055475 and autorun by the macro ( VirusTotal ) Payload Security C2 are 51.255.107.6/message.php and 81.177.27.222/message.php
Previous campaigns over the last few weeks have delivered numerous different download sites and malware versions. There are frequently 5 or 6 and even up to 150 download locations on some days, sometimes delivering the exactly same malware from all locations and sometimes slightly different malware versions. Dridex /Locky does update at frequent intervals during the day, sometimes as quickly as every hour, so you might get a different version of these nasty Ransomware or Banking password stealer Trojans.
All the alleged senders, companies, names of employees, phone numbers, amounts, reference numbers etc. mentioned in the emails are all innocent and are just picked at random. Some of these companies will exist and some won’t. Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found .
The bad guys choose companies, Government departments and other organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
This email attachment contains what appears to be a genuine word doc or Excel XLS spreadsheet with either a macro script or an embedded OLE object that when run will infect you.
Modern versions of Microsoft office, that is Office 2010, 2013, 2016 and Office 365 should be automatically set to higher security to protect you.
By default protected view is enabled and macros are disabled, UNLESS you or your company have enabled them. If protected view mode is turned off and macros are enabled then opening this malicious word document will infect you, and simply previewing it in windows explorer or your email client might well be enough to infect you. Definitely DO NOT follow the advice they give to enable macros or enable editing to see the content.
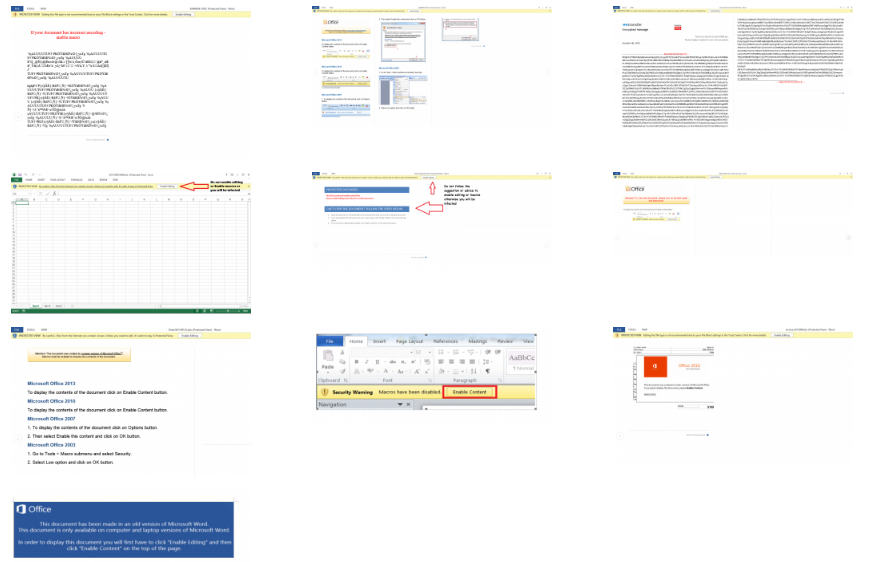
Most of these malicious word documents either appear to be totally blank or look something like these images when opened in protected view mode, which should be the default in Office 2010, 2013, 2016 and 365. Some versions pretend to have a digital RSA key and say you need to enable editing and Macros to see the content. Do NOT enable Macros or editing under any circumstances.
What Can Be Infected By This
At this time, these malicious macros only infect windows computers. They do not affect a Mac, IPhone, IPad, Blackberry, Windows phone or Android phone.
The malicious word or excel file can open on any device with an office program installed, and potentially the macro will run on Windows or Mac or any other device with Microsoft Office installed.
BUT the downloaded malware that the macro tries to download is windows specific, so will not harm, install or infect any other computer except a windows computer. You will not be infected if you do not have macros enabled in Excel or Word. These Macros do not run in “Office Online” Open Office, Libre Office, Word Perfect or any other office program that can read Word or Excel files.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware. Also please read our post about word macro malware and how to avoid being infected by them
Be very careful with email attachments. All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. It might be a simple message saying “look at this picture of me I took last night” that appears to come from a friend. It might be a scare ware message that will make you open the attachment to see what you are accused of doing.
Frequently it is more targeted at somebody ( small companies etc.) who regularly receive PDF attachments or Word .doc attachments or any other common file that you use every day, for example an invoice addressed to [email protected].
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets. Many of us routinely get Word, Excel or PowerPoint attachments in the course of work or from companies that we already have a relationship with.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. A lot of malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name.
Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types. Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball”, an invoice or receipt from some company for a product or service or receive a Word doc or Excel file report that work has supposedly sent you to finish working on at the weekend, you can easily see if it is a picture or document & not a malicious program. If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
With these malformed infected word, excel and other office documents that normally contain a vba macro virus, the vital thing is do not open any office document direct from your email client or the web. Always save the document to a safe location on your computer, normally your downloads folder or your documents folder and scan it with your antivirus.
Many Antiviruses do not natively detect vba macro-viruses in real time protection and you need to enable document or office protection in the settings. Do not rely on your Anti-Virus to immediately detect the malware or malicious content. DO NOT enable editing mode or enable macros
All modern versions of word and other office programs, that is 2010, 2013, 2016 and 365, should open all Microsoft office documents that is word docs, excel files and PowerPoint etc that are downloaded from the web or received in an email automatically in “protected view” that stops any embedded malware or macros from being displayed and running.
Make sure protected view is set in all office programs to protect you and your company from these sorts of attacks and do not over ride it to edit the document until you are 100% sure that it is a safe document. If the protected mode bar appears when opening the document DO NOT enable editing mode or enable macros the document will look blank or have a warning message, but will be safe.
Be aware that there are a lot of dodgy word docs spreading that WILL infect you with no action from you if you are still using an out dated or vulnerable version of word. This is a good reason to update your office programs to a recent version and stop using office 2003 and 2007.
Many of us have continued to use older versions of word and other office programs, because they are convenient, have the functions and settings we are used to and have never seen a need to update to the latest super-duper version. The risks in using older version are now seriously starting to outweigh the convenience, benefits and cost of keeping an old version going.
I strongly urge you to update your office software to the latest version and stop putting yourself at risk, using old out of date software.
