Yet another fake or spoofed DHL delivery notification delivering what today turns out to be Remcos RAT .
An email with the subject of “READ : (DHL Express) -Delivery Address Confirmation” Pretending to come from [email protected] <[email protected]> with a link in the email to download a word doc that in turn will download & run Remcos Rat
They use email addresses and subjects that will entice a user to read the email and open the attachment. A very high proportion are being targeted at small and medium size businesses, with the hope of getting a better response than they do from consumers.
What makes this one slightly worse than usual is the location of the word doc. The criminals sending these are abusing the Box.com file storage & delivery system to deliver the malware. Box is seen as a legitimate hosting service so links to them generally don’t get blocked by mail filters or Antivruses.
Important Notice: Box.com have no way of reporting abuse of their services or malware on their system UNLESS you register an account with them & fill in a support ticket, That is something I am not prepared to do.
The link in the email to download the malicious word doc is
The domain sending the emails looks like it has been set up deliberately by the criminals to be used in malware campaigns. It was registered on 15 March 2018 with all public details redacted for privacy.
dhllogisticservice.com currently behind Cloudflare, However as you can see from the email header section the emails were sent from dhllogisticservice.com on IP 89.46.222.157. I cannot see any website running on that IP address or domain. I get a 502 Cloudflare Error.
You can now submit suspicious sites, emails and files via our Submissions system
DHL-INVOICE-#18023.doc Current Virus total detections: | AnyrunApp | Hybrid Analysis |
Initially contacts which redirects to ( virustotal) which uses a vbScript to download the final malware payload from ( VirusTotal)
The email looks like:
From: [email protected] <[email protected]>
Date: Fri 26/10/2021 08:23
Subject: READ : (DHL Express) -Delivery Address Confirmation
Body Content:
Help Center
Confirm your Address for Delivery with DHL!
Dear Customer,
Your parcel (shipping document) arrived at the local post office.
Attached is your shipping document/invoice and copy of DHL receipt for your tracking which includes the new import/export policy supplied by DHL Express,
bill of lading and DHL tracking number
The DHL courier will modify your shipment information before shipping.
Label Number : CBD180938004576
Class : Package Services
Service(s) : Delivery Confirmation
Status : eNotification sent
P Please consider the environment before printing this emailCONFIDENTIAL NOTICE:This email, including any attachments, is confidential and may be privileged, and belongs to DHL Global Forwarding. If you are not the intended recipient, please do not read, copy, use nor disclose the contents of this communication to others. Please notify the sender immediately by replying to the email or by telephoning +62 21 5000 7000. Please delete the email and any copies of it thereafter.
DHL EXPRESS TEAM
———————
Important
• Ensure your packages are packed and labeled correctly to avoid damage or delays.
• Should you need to make changes to your pickup,download the file below.
© 2021 – All rights reserved.
Please do not reply to this email – inbox is not monitored.
Terms of Use | Privacy Notice | Terms and Conditions of Carriage
2021 © Deutsche Post AG
DHL INVOICE.DOC
326 kb
Download
Screenshot:
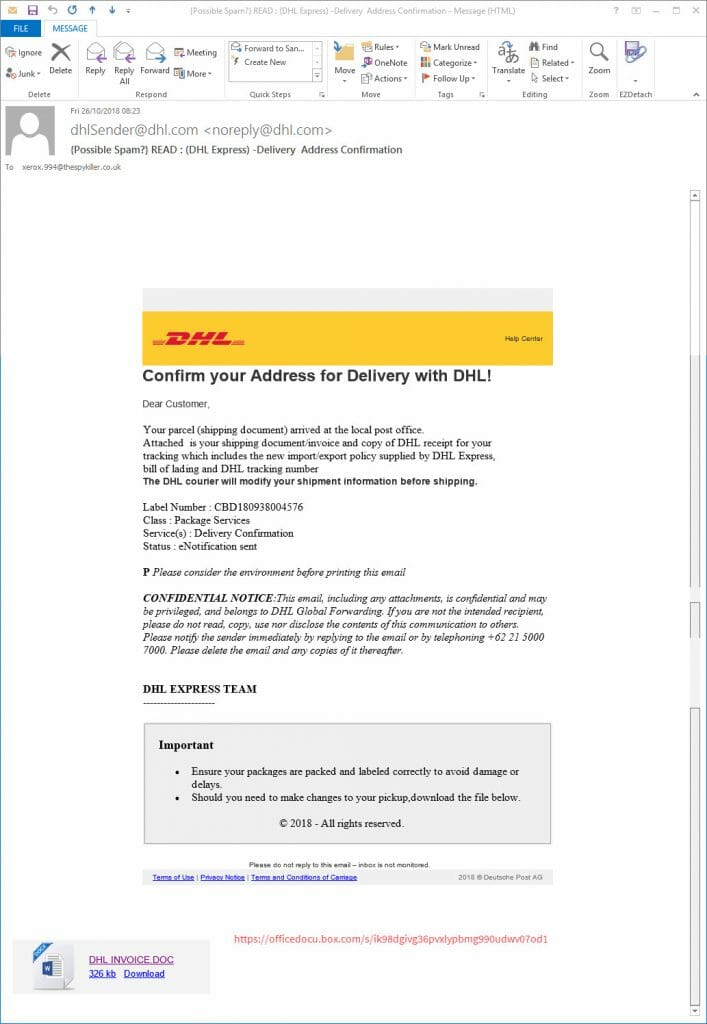
Fake DHL READ : (DHL Express) -Delivery Address Confirmation email
Email Headers:
| IP | Hostname | City | Region | Country | Organisation |
|---|---|---|---|---|---|
| 89.46.222.157 | slot0.dhllogisticservice.com | Timisoara | Timis | RO | AS48874 HOSTMAZE INC SRL-D |
Received: from [89.46.222.157] (port=42283 helo=slot0.dhllogisticservice.com) by My email server with esmtps (TLSv1.2:ECDHE-RSA-AES256-GCM-SHA384:256) (Exim 4.91) (envelope-from <[email protected]>) id 1gFwS3-00064s-DA for [email protected]; Fri, 26 Oct 2021 08:22:35 +0100 From: "[email protected]" <[email protected]> To: [email protected] Subject: READ : (DHL Express) -Delivery Address Confirmation Date: 26 Oct 2021 03:22:36 -0400 Message-ID: <[email protected]> MIME-Version: 1.0 Disposition-Notification-To: [email protected] Content-Type: multipart/related; boundary="----=_NextPart_000_0012_E7905D11.E3859B72"
All the alleged senders, amounts, reference numbers, Bank codes, companies, names of employees, employee positions, email addresses and phone numbers mentioned in the emails are all random. Some of these companies will exist and some won’t. Don’t try to respond by phone or email, all you will do is end up with an innocent person or company who have had their details spoofed and picked at random from a long list that the bad guys have previously found. The bad guys choose companies, Government departments and organisations with subjects that are designed to entice you or alarm you into blindly opening the attachment or clicking the link in the email to see what is happening.
Please read our How to protect yourselves page for simple, sensible advice on how to avoid being infected by this sort of socially engineered malware.
This is another one of the files that unless you have “show known file extensions enabled“, can easily be mistaken for a genuine DOC / PDF / JPG or other common file instead of the .EXE / .JS file it really is, so making it much more likely for you to accidentally open it and be infected.
Be very careful with email attachments. All of these emails use Social engineering tricks to persuade you to open the attachments that come with the email. Whether it is a message saying “look at this picture of me I took last night” and it appears to come from a friend or is more targeted at somebody who regularly is likely to receive PDF attachments or Word .doc attachments or any other common file that you use every day.
The basic rule is NEVER open any attachment to an email, unless you are expecting it. Now that is very easy to say but quite hard to put into practice, because we all get emails with files attached to them. Our friends and family love to send us pictures of them doing silly things, or even cute pictures of the children or pets.
Never just blindly click on the file in your email program. Always save the file to your downloads folder, so you can check it first. Many malicious files that are attached to emails will have a faked extension. That is the 3 letters at the end of the file name.
Unfortunately windows by default hides the file extensions so you need to Set your folder options to “show known file types. Then when you unzip the zip file that is supposed to contain the pictures of “Sally’s dog catching a ball” or a report in word document format that work has supposedly sent you to finish working on at the weekend, or an invoice or order confirmation from some company, you can easily see if it is a picture or document & not a malicious program.
If you see JS or .EXE or .COM or .PIF or .SCR or .HTA .vbs, .wsf , .jse .jar at the end of the file name DO NOT click on it or try to open it, it will infect you.
While the malicious program is inside the zip file, it cannot harm you or automatically run. When it is just sitting unzipped in your downloads folder it won’t infect you, provided you don’t click it to run it. Just delete the zip and any extracted file and everything will be OK.
You can always run a scan with your antivirus to be sure. There are some zip files that can be configured by the bad guys to automatically run the malware file when you double click the zip to extract the file. If you right click any suspicious zip file received, and select extract here or extract to folder ( after saving the zip to a folder on the computer) that risk is virtually eliminated.
Never attempt to open a zip directly from your email, that is a guaranteed way to get infected. The best way is to just delete the unexpected zip and not risk any infection.
