The latest version of these horrific porn related Sextortion, blackmail scams has changed slightly and pretends to be a message from a CIA employee who is part of the task force on paedophilia. There are multiple different senders and all the case numbers are different in each example received.
It states you are on the list to be investigated and are about to be arrested on 8th April 2019. However if you pay her $10,000 by bitcoin, before 27th March 2019, she will remove all your details from the database.
Of course this is a total fabrication. And just yet another slightly more inventive version of the Sextortion, blackmail scams we have been seeing for ages. All the attachments to the email just contain different copies of the CIA logo displayed at the bottom of the email
Every email that I have seen or been told about has a different individual bitcoin address. Whereas several emails have come from the same address.
Just ignore it & delete it.
From: Carlyn Blaine <[email protected]>
Date: Sun 17/03/2019 22:27
Subject: Central Intelligence Agency – Case #82956431
Body Content:
Case #82956431
Distribution and storage of pornographic electronic materials involving underage children.
My name is Carlyn Blaine and I am a technical collection officer working for Central Intelligence Agency.
It has come to my attention that your personal details including your email address ([email protected]) are listed in case #82956431.The following details are listed in the document’s attachment:
• Your personal details,
• Home address,
• Work address,
• List of relatives and their contact information.
Case #82956431 is part of a large international operation set to arrest more than 2000 individuals suspected of paedophilia in 27 countries.
The data which could be used to acquire your personal information:
• Your ISP web browsing history,
• DNS queries history and connection logs,
• Deep web .onion browsing and/or connection sharing,
• Online chat-room logs,
• Social media activity log.
The first arrests are scheduled for April 8, 2019.
Why am I contacting you ?I read the documentation and I know you are a wealthy person who may be concerned about reputation.
I am one of several people who have access to those documents and I have enough security clearance to amend and remove your details from this case. Here is my proposition.Transfer exactly $10,000 USD (ten thousand dollars – about 2.5 BTC) through Bitcoin network to this special bitcoin address:
33KEtZ8drCJTzh7z5yNLhK9s8bApRvsZS9
You can transfer funds with online bitcoin exchanges such as Coinbase, Bitstamp or Coinmama. The deadline is March 27, 2019 (I need few days to access and edit the files).Upon confirming your transfer I will take care of all the files linked to you and you can rest assured no one will bother you.
Please do not contact me. I will contact you and confirm only when I see the valid transfer.
Regards,
Carlyn Blaine
Technical Collection Officer
Directorate of Science and Technology
Central Intelligence Agency
Screenshot:
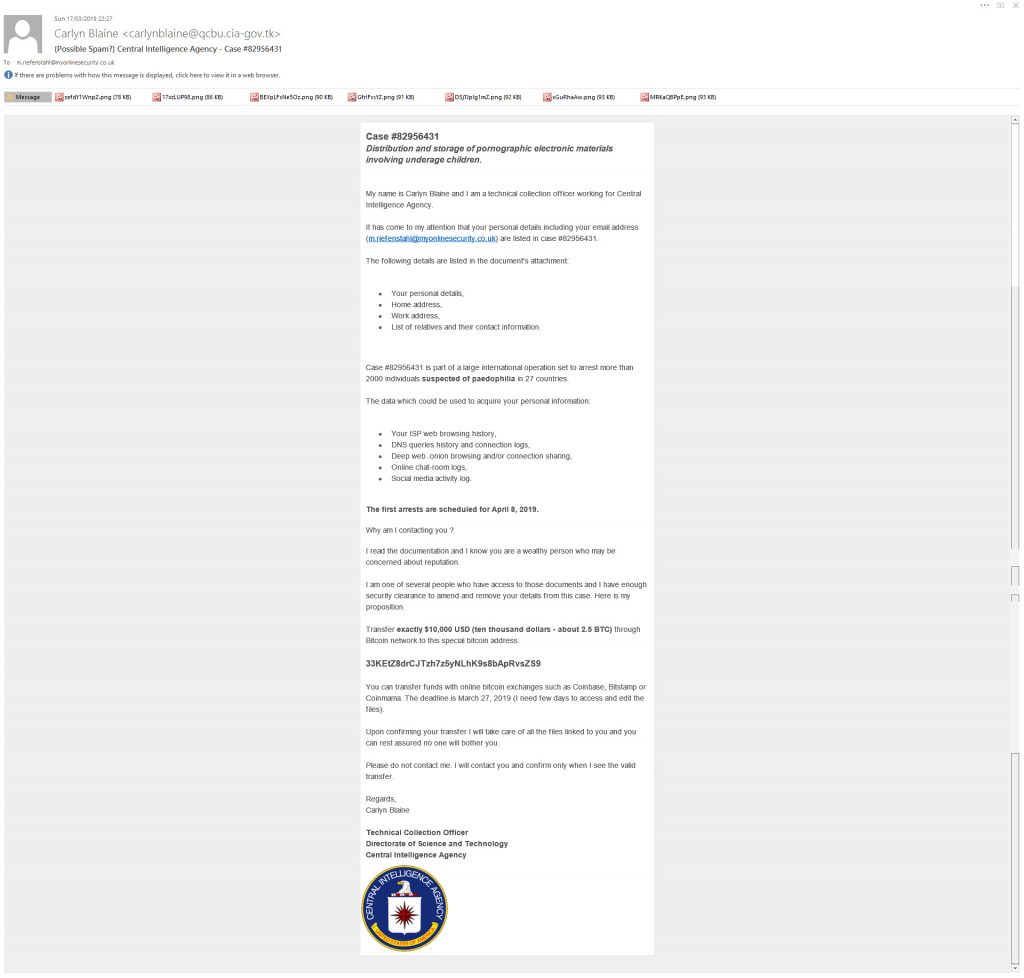 Fake CIA Sextortion Scam email
Fake CIA Sextortion Scam email
Some of the other email that I have seen include:
[email protected]
[email protected]
[email protected]
[email protected]
[email protected]
Other Bitcoin addresses in the emails include:
34TieKvg9Lpf5pSSWGaNvj1FbxY232aFAW
3Hu6RfvmeW1WM4yNisWmJhXzSjAbeaWK7n
33KEtZ8drCJTzh7z5yNLhK9s8bApRvsZS9
3JcBBN2bR9g5uW69ADWsjF8d7dKnZeW55x
3Gpte8gnfZV3qWgQgRWDqZLkUQZa4ToxQS
3JoV6VyMavsYFXkdtUdpmBvaDaEbuCjUH5
3DAEVKMXxAXH5njM2CZoV4U7QdK7Sf6ZZZ
39BXj6HzMfYh3ZtLvYX5igxyjouqW4ApvM
34STNDZPEUhZXcKheLZH9JPxhGZzRcXKvN
35mmTS61KfwobB2zhoZFGFpjJ8BgDRqMui
3AiFhFqKR2J6n3sw6ATcB7FeckiA5852rp
32VsS6uSr8Xx7SPMptDRKUexWpZFmLcDRx
37aet9CFoiZuWce28kVm7YKnwbhcD4qCCD
3KDNxsP5humqMRtEb3RB3tCrZByKbhuF7f
36M16gPhT3keBHUBBuLzDGW6wP5cFZdEg3
33NajP9kGsqQTaR7pvtLnxqxNtjNSVpF1c
383JRiH6fZFBwhafBLgeRJf76iuGUgWehK
36qxWU2hhfGE2fFHd6y8d6UkRMXzZZUNWz
3CTDecaTpZDo72SeAscEsUMUE2r2uPpVWj
35kTRsgvw9VsHzmi1Qr9qWY7kfpupjLMQk
3D9MAGYDZoS82jX8kUnfiR1VW4Ek34ehzQ
33486HJsk4rc6qdzFoF7sGFE68rQwkdUNo
3G5KjxZi9HhutFFFBeb97yasvCDFktvTdn
3DsQPYEFM6ibbCPs1V4m3r7aXCpFw8nS3N
3HNeAn79k7SwxqbRoFV2QM6h9VNfHVZifQ
3LnsCt6nFpf3wVzuiTtbyrTCQSo92GtYvD
3MSsQswLWRkqHshgByGscy3h4adTXZ6bCE
3KA7C3mmbPnSosc7ceGRuHCB2LySn5sLFq
3PUvWaAxz4WkteqrE9bMNPwKt3ZYVqg5Li
3JKmhpRgVB8kmRARUQ2fJ9qyMWur5kkvwh
3E6MXgMNKa39YAvih7fPcCDBdM1G3Bbx7M
3CnyymSUaB3CxPeDSBUK3YsZAC5sidZN83
3GbSfCmG3wvgM9jeTWbk7pUELajuDvQuqB
3QJ4B1e4GVRVoxLrSQC6XSWHAuXDwsx2Da
33TFVDGoWHcnagXoixLStjPBuAABCZZUQL
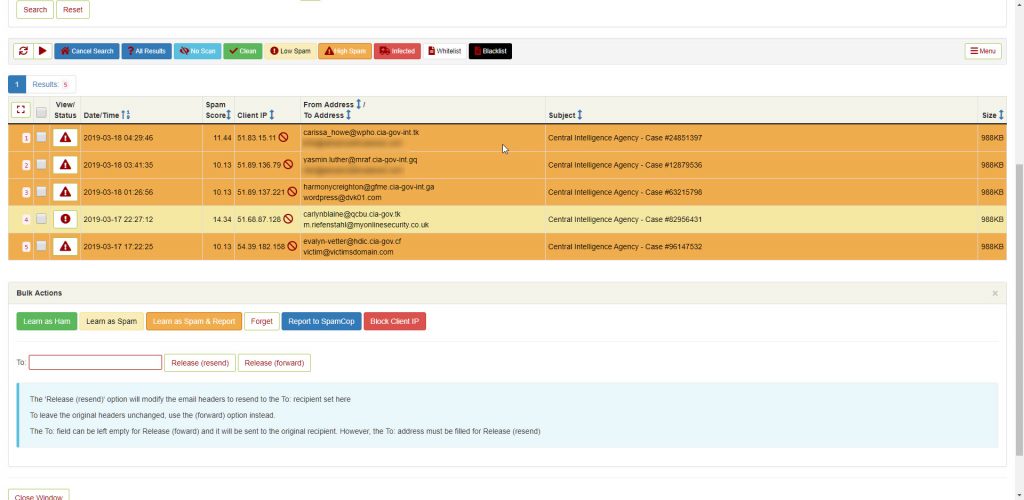
Fake CIA sextortion scam email list
These all come from a range of IP addresses on OVH
| IP | Hostname | City | Region | Country | Organisation |
|---|---|---|---|---|---|
| 51.83.15.11 | mx.wpho.cia-gov-int.tk | Roubaix | Nord-Pas-de-Calais | FR | AS16276 OVH SAS |
| 127.0.0.1 | Local IP | ||||
51.83.15.11
51.89.136.79
51.89.137.221
51.68.87.128
54.39.182.158
What To Do When You Receive A Blackmail, Sextortion Scam Email
If you do receive any email like this, Don’t panic, Do not respond to it, contact the appropriate police /fraud authority in your country, follow the advice on their site to report this crime and then delete the email from your computer.
- In UK use Action Fraud
- If you are in USA then use the FBI IC3 report site.
- In Australia use ScamWatch
- Anywhere in EU see europol for country contacts
- In Switzerland use https://stop-sextortion.ch/en/index.html
- Most other countries worldwide will have a similar method of reporting these sextortion, blackmail, scam attempts.
- You can also report the bitcoin wallet number to the Bitcoin abuse system. This list is used by law enforcement and researchers to monitor transactions and hopefully catch the criminals when they slip up & spend the money or move the money to a bank account etc.
From a very quick domain search it looks like all these domains have had numerous subdomains and then email addresses on the subdomains created and used in this scam, There are probably other variations of these free domains that I haven’t yet found.
gov-cia.gq
gov-cia.ml
gov-cia.tk
gov-cia.cf
gov-cia.ga
gov-cia-it.tk
gov-cia-it.cf
gov-cia-it.ml
gov-cia-it.gq
gov-cia-it.ga
cia-gov-it.cf
cia-gov-it.ml
cia-gov-it.cf
cia-gov-it.gq
cia-gov-int.ga
cia-gov-int.tk
cia-gov-int.gq
cia-gov-int.ml
cia-gov-int.cf
ciagov.cf
ciagov.ml
ciagov.gq
ciagov.tk
ciagov.ga
cia-us-govn.ml
cia-us-govn.cf
cia-us-govn.gq
cia-us-govn.tk
cia-us-govn.ga
cia-int.gq
cia-int.cf
cia-int.ml
cia-int.tk
cia-int.ga
cia-gov.tk
cia-gov.cf
cia-gov.gq
cia-gov.ga
cia-gov.ml
